The way people talk about privacy failures is always dramatic. A breach. A leak. A giant database suddenly floating around the internet. One ugly moment where everyone can point and say that’s when the system collapsed.
I used to think about it the same way.
But while I was reading through Midnight Network discussions the other night a different version of failure kept bothering me. Not the loud kind. The quiet one that doesn’t look like failure at all when it’s happening.
Imagine a team launching a private workflow. Good intentions careful design the whole thing built around selective disclosure. Users reveal only what they need to reveal. Counterparties see enough to move forward nothing more. For the first few months everything works exactly the way a privacy-first system is supposed to work.
Then the product starts touching the real world.
A payment gets flagged and someone from compliance wants a little more context before approving it. Nothing dramatic. Just one extra field that makes the review easier. A partner institution asks for slightly richer transaction metadata because it helps their reconciliation process. Later the support team wants a broader view during certain disputes because debugging private workflows can be slow.
Infographic: Flowchart showing incremental disclosure creep over time in applications
Every change feels reasonable.
That’s the strange part.
No one wakes up and says let’s weaken the privacy model today. The conversation always sounds practical. Faster investigations. Cleaner reporting. Fewer support tickets. The kind of small operational improvements every product team makes once real users start pushing against the edges of the system.
I’ve watched enough products evolve to know how that story usually goes.
Six months later the workflow still calls itself private but the disclosure surface is wider than it was at launch. Maybe not dramatically wider but noticeably different if you compare the two versions side by side. The boundary moved a little here a little there and nobody remembers the exact meeting where the original line changed.
The interesting thing is that none of this requires the protocol to fail.
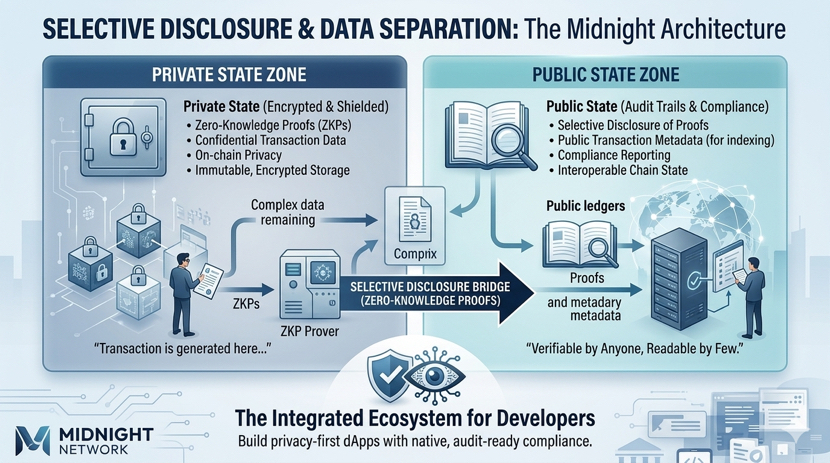
Systems based on Zero-Knowledge Proof can still verify every rule perfectly. The cryptography does its job. The proofs check out. Transactions clear. From the network’s perspective everything is behaving exactly the way it should.
And yet the experience of privacy inside the application can slowly change anyway.
That possibility is what I keep circling back to when I think about Midnight. The technology itself is built to make selective disclosure practical. That’s the whole point. Developers can design workflows where sensitive data stays local while the network verifies the outcome.
But selective disclosure isn’t a fixed wall.
It’s a line that product teams draw.
And lines drawn by humans tend to move once the pressure of real products shows up. New partners arrive. Regulators ask questions. Support teams need better visibility. Product managers want smoother user experiences. Each adjustment feels harmless on its own.
Infographic: Illustration of proof verification process versus local data storage
Put enough of those adjustments together and the shape of the system quietly changes.
I’m not saying that’s inevitable. Plenty of teams care deeply about protecting their privacy boundaries. Still I’ve seen enough software evolve over time to know how easy it is for the definition of just enough disclosure to drift.
That’s why I think the real challenge for Midnight won’t be proving that private smart contracts can work. The cryptography already shows that they can.
The harder challenge might be cultural.
Whether the developers building on the network keep treating that privacy boundary like a boundary even when the easier path is to stretch it a little further every time the product hits friction.
Because the version of failure I worry about most isn’t a catastrophic exploit.
It’s the one where the proofs still verify the contracts still run and the application still calls itself private but the line that once protected users has quietly moved so many times that nobody can clearly say where it started.
$NIGHT #night @MidnightNetwork
