I remember when I first started paying attention to identity projects in crypto, I assumed adoption would happen almost automatically. The idea felt too obvious to ignore. If users could finally control their own identity instead of relying on platforms, then usage should follow. At the time I believed the narrative itself was strong enough. But after spending more time looking at how these systems actually function, I noticed a different pattern. Many projects either relied on hidden centralization or were too complex for normal users to engage with. That experience changed how I evaluate these ideas. Now I focus less on the concept and more on whether the system can realistically operate at scale without creating friction.
That shift in thinking is why #SignDigitalSovereignInfra caught my attention. Not because digital identity is a new story, but because it raises a more practical question. Can identity infrastructure be both user-controlled and verifiable across multiple environments without depending on a central authority. That is where most systems struggle. So the real question becomes whether this model can move beyond theory and become something developers and users actually rely on in everyday interactions.From what I understand, the protocol is designed around verifiable identity that remains under user ownership. Instead of storing identity in a single database, it distributes trust through cryptographic proofs. This allows users to prove specific attributes without exposing unnecessary data. A simple way to think about it is like accessing multiple platforms with the same identity, but without handing over full control to each one. The system verifies what is required while keeping the rest private. This matters because it changes how data moves between applications. Instead of platforms owning identity, users carry it across ecosystems in a way that is both secure and interoperable.$EDGE and $UAI connect with Sign by enabling AI systems to generate, process, and validate identity-related data off-chain, while Sign ensures those identities remain user-owned, verifiable, and usable across different applications.
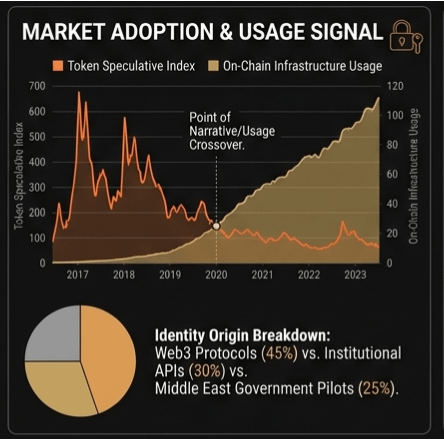
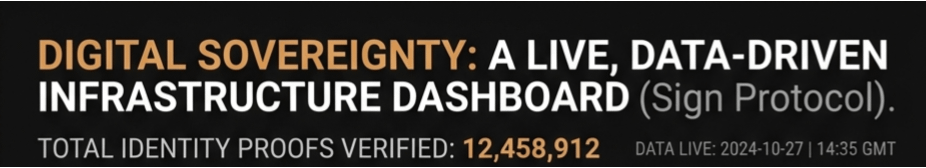
The token layer plays a role in aligning incentives between participants in this system. Validators are responsible for maintaining the integrity of identity proofs, while developers build applications that depend on these verifications. If the design works as intended, demand for the token should come from real usage rather than speculation alone. Every identity verification, every interaction that relies on credentials, contributes to network activity. That creates a more direct relationship between utility and value, which is something many identity-focused systems fail to achieve.There is also a broader angle that makes this more interesting. Sign can position itself as digital sovereign infrastructure not just for individuals, but as a foundational layer for regions that are actively building digital economies. In the context of Middle East economic growth, where governments and institutions are investing heavily in digital transformation, having a system that enables secure and verifiable identity across sectors could become highly relevant. It allows businesses, users, and institutions to interact within a trusted framework without relying on fragmented or centralized identity providers. This shifts the conversation from a niche crypto use case to something that can support real economic coordination.
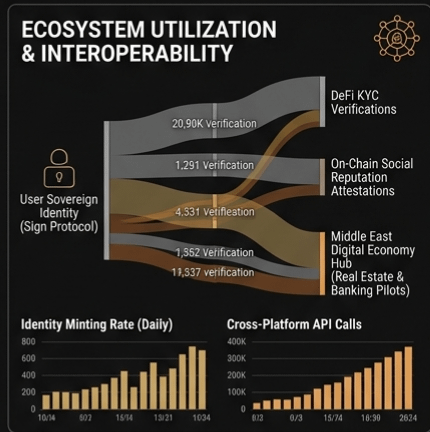
Looking at the market side, it appears the project is still in an early phase where attention is forming but not fully stable. Price behavior and trading volume suggest that interest tends to increase during narrative cycles rather than through consistent usage. Holder growth can indicate rising awareness, but it does not necessarily confirm that users are actively engaging with the system. In situations like this, the market is usually pricing future expectations rather than current demand. That gap between narrative and execution becomes one of the most important variables to monitor.But this is where the real test appears. The biggest challenge is not the idea of digital sovereignty. It is sustained usage. Because if developers do not build applications that rely on this identity layer in a meaningful way, the system risks becoming infrastructure without traffic. And if users do not repeatedly use their identity across platforms, the network does not generate the activity required to justify its design. On the other hand, if applications begin integrating identity into real workflows and users start interacting with them regularly, the system can strengthen over time. Usage would drive value, and value would attract more development.
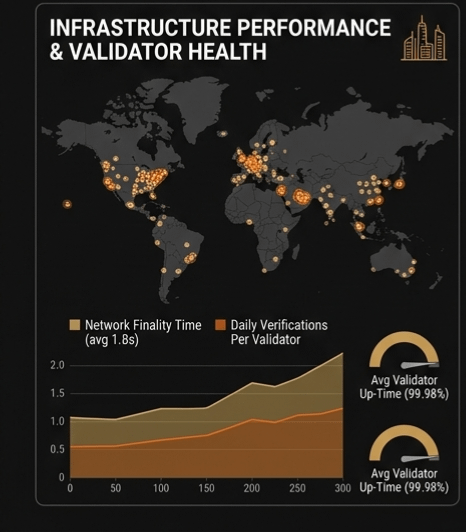
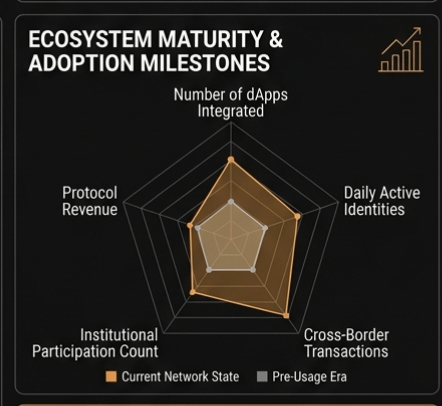
What would make me more confident is not short-term price movement but consistent signals of adoption. I would want to see developers building products where identity is essential rather than optional. I would also look for increasing frequency of identity-based interactions, which would suggest users are relying on the system in practice. Growth in validator participation would indicate confidence in maintaining the network. At the same time, I would become more cautious if activity remains driven primarily by speculation or if developer momentum slows after the initial wave of attention.So if you are watching this project, it probably makes more sense to focus on how often identities are actually being created and used rather than how the token behaves in the short term. In markets like this, strong narratives can attract attention quickly, but they rarely sustain systems on their own. The difference between an idea that sounds powerful and infrastructure that actually matters usually comes down to one thing. People have to keep using it when the initial excitement fades.