A new wave of cyber theft shows how strategy has replaced scale
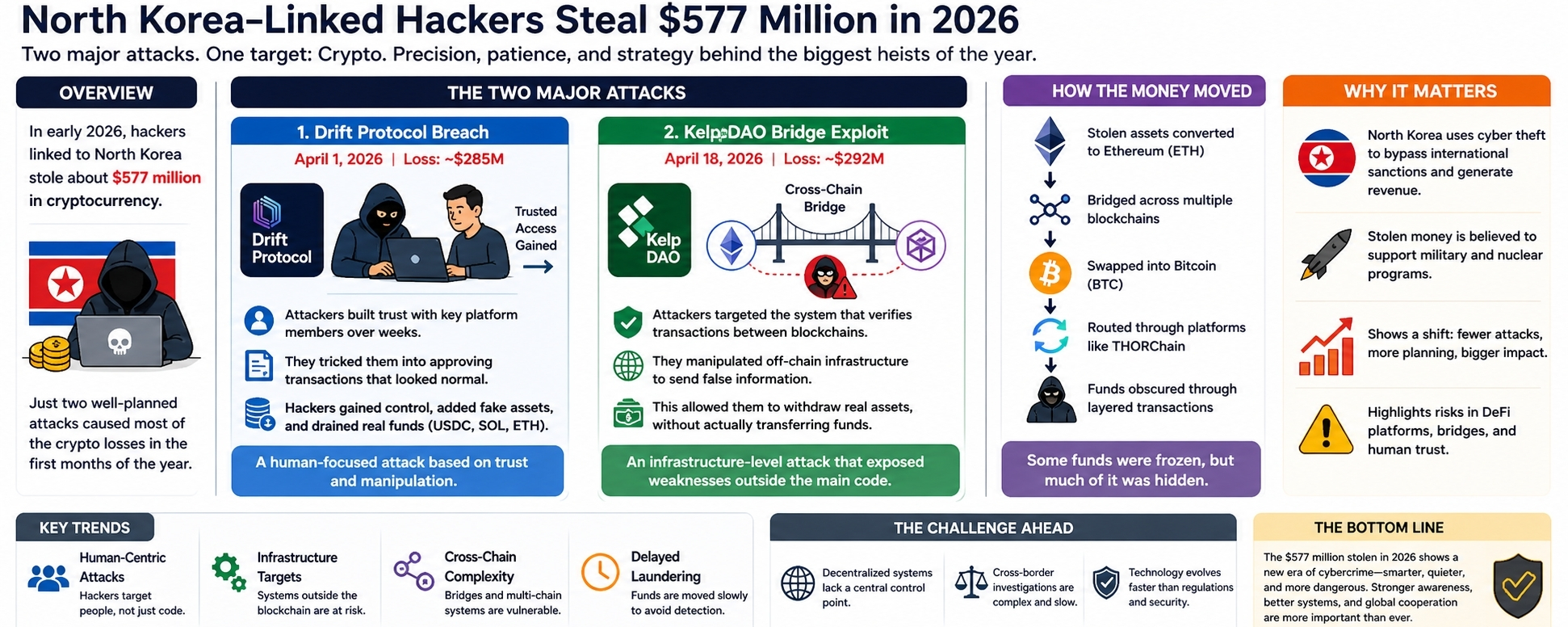
In early 2026, cybersecurity analysts traced about $577 million in stolen cryptocurrency to hacking groups linked to North Korea. What stands out is not just the amount, but how it was stolen. Instead of carrying out dozens of smaller attacks, these groups focused on just two carefully planned operations—and that was enough to dominate global crypto losses for the year’s first months.
This shift signals a clear change in approach. Groups such as the are no longer relying on frequent attacks. They are choosing precision, patience, and deep planning to achieve bigger results with fewer moves.
Two attacks that shaped the year
The Drift Protocol breach
The first major incident happened on April 1, 2026, when Drift Protocol lost around $285 million.
This was not a typical hack involving broken code. Instead, it was built on trust. Attackers spent time interacting with key individuals who had control over the platform. By gaining their confidence, they convinced them to approve transactions that looked normal but were actually harmful.
Those approvals gave hackers the access they needed. From there, they quietly took control, inserted fake assets, and drained real funds from the system.
What makes this attack important is how human it was. No complex exploit was needed—just patience and manipulation.
The KelpDAO bridge exploit
Just over two weeks later, on April 18, another major attack hit KelpDAO, leading to losses of about $292 million.
This time, the target was not people, but infrastructure. The attackers focused on the system that verifies transactions between blockchains. By interfering with that process, they made it appear as if funds had been legitimately moved when they had not.
That false signal allowed them to withdraw real assets.
This kind of attack highlights a growing issue in crypto systems: even if the main code is secure, the supporting systems around it can still be vulnerable.
Moving the money
After the thefts, the stolen assets did not stay in one place for long. They were quickly shifted across different networks and converted into other cryptocurrencies.
A significant portion moved through platforms like THORChain, which allow users to swap assets across blockchains without relying on centralized exchanges.
Some funds were frozen by security teams, but much of it was successfully moved and hidden through layered transactions. This makes recovery extremely difficult.
Why these attacks matter
These operations are not just about money. North Korea faces strict international sanctions, limiting its access to global finance. Cyber theft has become a way to generate funds outside those restrictions.
That means the impact goes beyond the crypto industry. The money is believed to support state programs, including military development.
A clear pattern is emerging
Several trends can be seen from these incidents.
First, attacks are becoming more focused on people. Instead of breaking systems, hackers are learning how to influence decisions.
Second, infrastructure is now a key target. Systems that connect blockchains or verify transactions are under increasing pressure.
Third, the movement of stolen funds is becoming more advanced. By spreading assets across chains and platforms, attackers make tracking much harder.
Finally, patience is playing a bigger role. Some funds are left untouched for a period before being moved, reducing immediate detection.
The challenge ahead
Security teams, governments, and blockchain projects are working to respond, but the challenge is complex.
Decentralized systems do not have a single point of control. Attacks often cross multiple jurisdictions. And as technology evolves, so do the methods used to exploit it.
The events of 2026 show that the biggest risks may no longer come from obvious technical flaws, but from subtle weaknesses in how systems and people interact.
Conclusion
The $577 million stolen in early 2026 is not just a headline figure. It reflects a deeper shift in how cyber attacks are carried out.
Fewer attacks, more planning, and smarter execution are defining this new phase. Whether targeting human trust or technical infrastructure, North Korea-linked hackers have shown that they can adapt quickly and strike effectively.
The lesson is clear: defending the future of digital finance will require more than stronger code. It will require stronger awareness, better systems, and constant vigilance.