1. Introduction: The Shift from Passive Security to Active Defense
In the high-stakes theater of modern finance, digital asset security has transcended the realm of technical "tips" to become a fundamental pillar of financial sovereignty. To participate in the crypto economy is to undergo a paradigm shift: moving from a traditional "hope-based" security model—where institutional intermediaries bear the burden of protection—to an "architecture-based" model. In this decentralized landscape, the individual is not merely a user; they are the ultimate gatekeeper and sovereign custodian of their wealth.
This shift in responsibility necessitates a professional-grade approach to Operational Security (OpSec). In a semi-centralized ecosystem, the blockchain protocol itself is rarely the point of failure; rather, the interface between the user and the platform serves as the primary attack vector. A robust security posture recognizes that human error and interface vulnerabilities are the greatest risks. By establishing a disciplined strategic framework, users move beyond reactive patches to build a proactive defense-in-depth system designed to preserve asset integrity against an increasingly sophisticated threat landscape.

2. Beyond the Password: Evaluating the Multi-Layered Authentication Stack
The strategic reality of digital assets renders traditional password-only systems obsolete. In an environment where transactions are irreversible and 24/7, a single point of failure is an unacceptable risk. Securing the account entry point requires a multi-layered authentication stack that prioritizes cryptographic proof over vulnerable legacy communication channels.
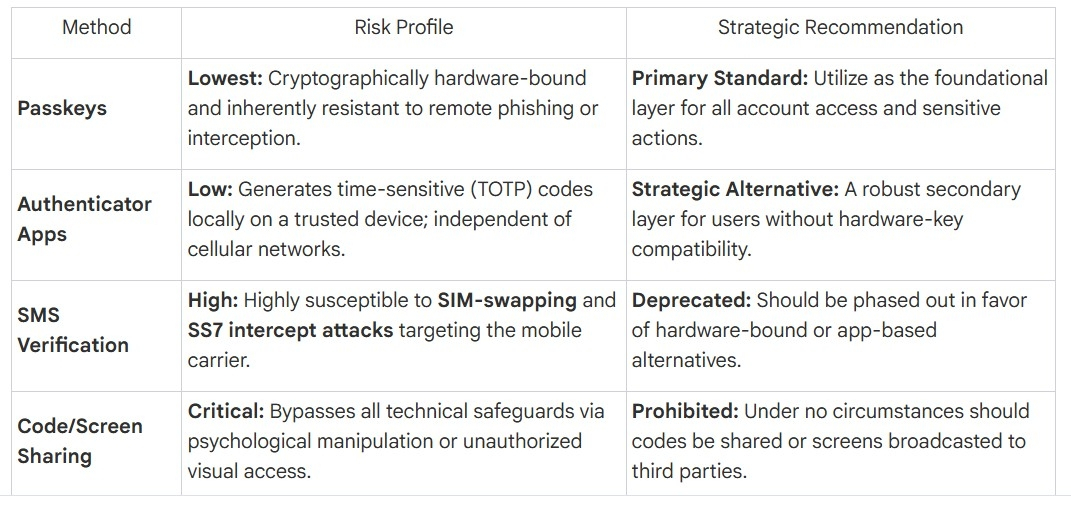
A sophisticated strategist must differentiate between Second Factor Authentication (2FA) methods based on their underlying technical vulnerabilities. While SMS-based verification offers convenience, it is fundamentally flawed due to its reliance on the legacy telecommunications infrastructure. Conversely, Passkeys and Authenticator Apps provide a significantly higher security ceiling by ensuring that the authentication factor remains hardware-bound or locally generated, isolated from network-level interception.
The Hierarchy of Authentication Security
While authentication secures the "front door," technical settings are the critical failsafe for when authentication is bypassed. The integrity of the "vault" is determined by internal governance.
3. Hardening the Perimeter: Whitelisting and API Governance
A strategic security posture requires the systematic reduction of the "attack surface." By implementing restrictive configurations, a user ensures that even in the event of a credential or 2FA compromise, the mobility of assets remains strictly governed by pre-verified logic.
Strategic Isolation: The Unique Email Protocol
The email account linked to a digital asset platform is the primary recovery vector and a critical point of failure. A professional-grade strategy requires Email Isolation: the use of a unique, dedicated email address exclusively for the exchange account. This isolates the account from phishing attempts sent to general-purpose personal or work emails and ensures that a compromise in one’s social or professional life does not grant an attacker a direct path to their financial recovery tools.
Withdrawal Whitelisting
"Withdrawal Whitelisting" transforms an account from a liquid target into a restricted environment. Once enabled, assets can only be transferred to addresses that have been pre-verified and aged within the system. This creates a high-friction environment for attackers; even with full account access, they cannot immediately siphoning funds to unknown destinations, providing the defender with the vital window of time necessary to initiate emergency protocols.
Protocol for API Governance
For users utilizing automated tools, API keys must be treated with the same level of secrecy as a master password.
Zero Third-Party Sharing: Strict prohibition against sharing API keys with third-party "portfolio managers" or "trading bots." These are high-risk vectors for unauthorized liquidation or asset diversion.
Removal of Latent Access: Periodically audit and immediately remove any unused or unnecessary API keys to minimize potential entry points.
Conservative Permissions: Implement the principle of "Least Privilege." Never grant "Withdrawal" permissions to an API key unless absolutely necessary for a specific, air-gapped workflow.
Informed Implementation: Never generate an API key without a comprehensive understanding of its function and the specific risks it introduces to the account architecture.
4. The Social Engineering Battlefield: Counter-Phishing and Verification Protocols
Modern asset theft is more frequently a result of deception (social engineering) than technical breaches of the exchange infrastructure. Attackers exploit the human element, utilizing "spoofed" communications that mimic official branding to bypass technical defenses.
A strategist must recognize that visual authenticity is a fallible metric. Logos, sender names, and professional formatting can be easily spoofed in emails and SMS. To counter this, users must utilize a "Verification Stack" to establish an immutable "Source of Truth."
Inviolable Rules for Verification
Anti-Phishing Codes: Enable a unique, user-defined code that must appear in the header of every official email. The absence of this code is an immediate indicator of a fraudulent communication.
Binance Verify Protocol: Utilize the "Binance Verify" tool as the final arbiter for truth. Before interacting with any website, email address, or social media handle claiming to be official, verify it through this tool.
Official Channel Discipline: Acknowledge that the platform will never initiate contact via WhatsApp or unsolicited social media messages to request payments, sensitive data, or device access.
Domain Hygiene: Manually inspect every URL and domain before clicking. Always access the platform via bookmarked official domains or the official application.
5. Environmental Integrity: Securing the Access Point
Technical settings are moot if the underlying operating system or network is inherently compromised. A "Clean Room" approach ensures that the physical and digital environment used to access wealth is untainted by hidden observers.
Inviolable Rules for Device Hygiene
Network Sovereignty: Avoid all public Wi-Fi networks. Access accounts only via secured, private networks that you control.
Official Software Lineage: Only install applications from verified, official marketplaces. Third-party repositories are notorious for hosting "Trojanized" versions of financial apps.
Exclusion of Browser Extensions: Browser extensions operate with permissions to read and modify website data, making them potent "man-in-the-browser" vectors for session hijacking and form-grabbing. Avoid all extensions on the browser used for financial transactions.
Active Defense Layer: Maintain updated, professional-grade Anti-Virus and Anti-Malware software. Regular, deep scans are mandatory to detect undetected Trojans that can bypass standard 2FA by capturing session data at the point of entry.
The "So What?" of device security is simple: if the underlying OS is compromised, an attacker can see what you see and type what you type, rendering even the strongest 2FA secondary to the malware's control.
6. Tactical Response: The User-Initiated Emergency Freeze and Liability Realities
In the event of a suspected breach, the difference between a minor incident and a catastrophic loss is measured in seconds. Every strategic framework must include a "Zero-Hour" response plan to regain control of the environment.
The Emergency Protocol
If you detect abnormal activity—such as unauthorized login notifications, unauthorized changes to 2FA, or modifications to your withdrawal whitelist—you must execute the following immediately:
User-Initiated Emergency Freeze: Navigate to the official interface and use the "Disable Account" feature. This acts as a global kill switch, freezing all trades and withdrawals instantly.
Official Channel Reporting: Immediately report the incident through the official customer support channel to initiate a formal investigation and forensic audit.
The Realities of Liability
In the crypto era, the user bears the ultimate financial risk for security failures. The exchange acts as a provider of sophisticated defensive tools, but it does not function as an insurer for personal negligence or the failure to secure one's own recovery vectors (such as email). Any activity occurring under a user's account—including losses resulting from spoofed communications or compromised devices—remains the legal and financial responsibility of the user.
7. Closing Reflection: The Evolution of Responsibility in a Mature Market
As the digital asset market matures and institutional-grade participation becomes the norm, the era of the "amateur" crypto user must come to an end. The casual security habits that defined the early industry are no longer compatible with a high-stakes global ecosystem where assets are targeted by sophisticated state-sponsored and criminal actors.
Individual security hygiene is not merely a personal choice; it is the bedrock upon which the credibility and stability of the entire digital asset class are built. By adopting a disciplined, strategic architecture for custody, users do more than protect their own wealth—they contribute to the maturation of the broader market. In this landscape, the cost of negligence is absolute. However, the peace of mind afforded by a professional-grade, proactive security architecture is the ultimate asset for any serious participant in the crypto era.
