The network's economic security model combines Proof-of-Work (PoW) and Proof-of-Stake (PoS) mechanisms to create sustainable incentives for honest verification while capturing and distributing real economic value. This hybrid approach addresses unique challenges in verifying AI outputs.
The network generates tangible economic value by reducing AI error rates through verification. Customers pay network fees to obtain verified output, and the network distributes these fees to participants—node operators and data providers—through verification rewards.
Unlike traditional blockchain networks where PoW involves solving cryptographic puzzles with infinitesimally low probability of random success, the Mira network transforms verification into standardized multiple-choice questions.
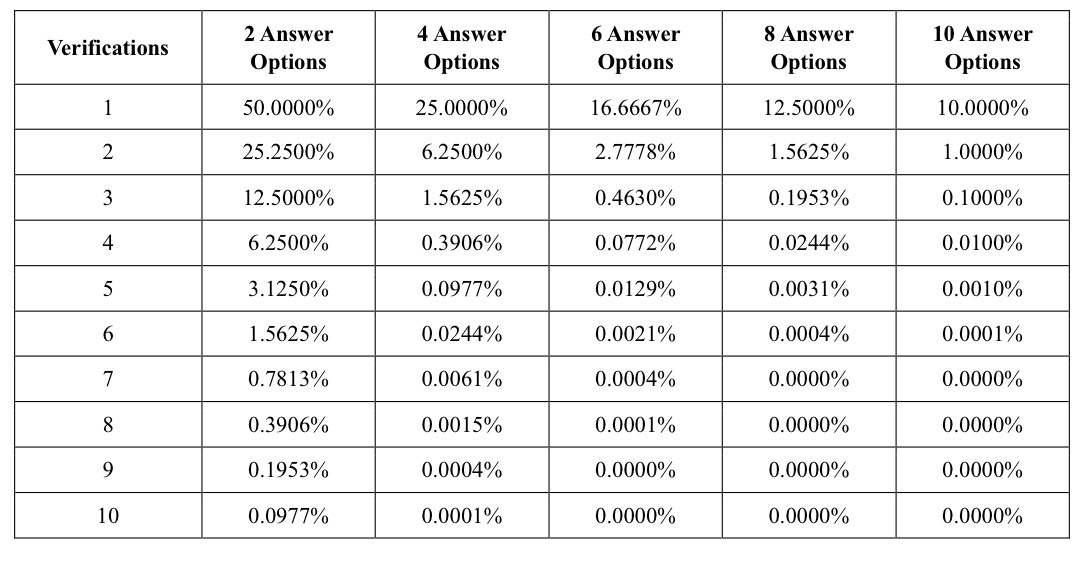
While this standardization enables systematic verification across nodes, it also creates a fundamental challenge: the probability space of possible responses is constrained. For instance, a verification task will have a 50% chance of random success with binary choices, or 25% with four options. This makes random guessing a potentially attractive strategy, offering high reward for no computational cost.
To mitigate this, nodes must stake value to participate in verification. If a node consistently deviates from consensus or demonstrates patterns suggesting random responses rather than actual inference, their stake can be slashed. This economic penalty ensures that attempting to game the system through random responses becomes economically irrational.
The network's economic security model thus operates on three foundational principles. First, node operators behave rationally in response to economic incentives, as their staked value is at risk through slashing penalties. Second, network security is maintained as long as honest operators control the majority of staked value, making manipulation attempts prohibitively expensive. Third, as the network scales, the natural diversity of verifier models reduces statistical bias, as different models bring varied training approaches and knowledge bases. These principles reinforce each other: economic incentives attract diverse participants, whose varied perspectives strengthen security, which in turn supports the economic model.
Table 1 illustrates the probability of successfully guessing the correct answer given the number of answer choices
During the network's initial phase, node operators are carefully vetted to ensure network integrity. In the second phase, the network will begin to decentralize with designed duplication, where multiple instances of the same verifier model process each verification request. This duplication, while increasing verification costs, enables robust identification of malicious or lazy operators. As the network matures into its steady-state, verification requests are randomly sharded across nodes, making collusion increasingly difficult and expensive.
The network's sharding mechanism provides another layer of security: by studying response patterns and similarity metrics across nodes, the system can identify potential collusion. Malicious actors would need to control a significant portion of the network's staked value to influence outcomes, at which point their economic incentives align with honest operation.
Node operators might attempt to game the network through various strategies, such as maintaining databases of common verification results to shortcut the verification process. In the short term, the diversity and uniqueness of verification requests make such caching strategies ineffective. At scale, the existence of a large corpus of verified facts presents opportunities for derivative protocols that leverage the network's verification capabilities.
Node operators achieve success by reaching correct answers at the lowest cost. When specialized models achieve comparable performance to larger models on specific verification tasks, this creates legitimate optimization opportunities. These opportunities drive the development of efficient, task-specific models optimized for particular domains, benefiting the entire ecosystem through higher accuracy rates, lower costs, and reduced latency.
The network's economic model reinforces these positive dynamics through multiple reinforcing cycles. As network usage grows, increased fee generation enables better verification rewards, attracting more node operators and driving improvements in accuracy, cost, and latency. This growth strengthens network security organically: stake requirements rise with network value, model diversity expands through both specialization and fundamental differences in perspective, and accumulated verification history enables increasingly sophisticated anomaly detection. These compounding effects create a robust game-theoretic equilibrium where honest verification and continuous innovation emerge as dominant strategies, while making malicious manipulation both economically irrational and technically infeasible.
