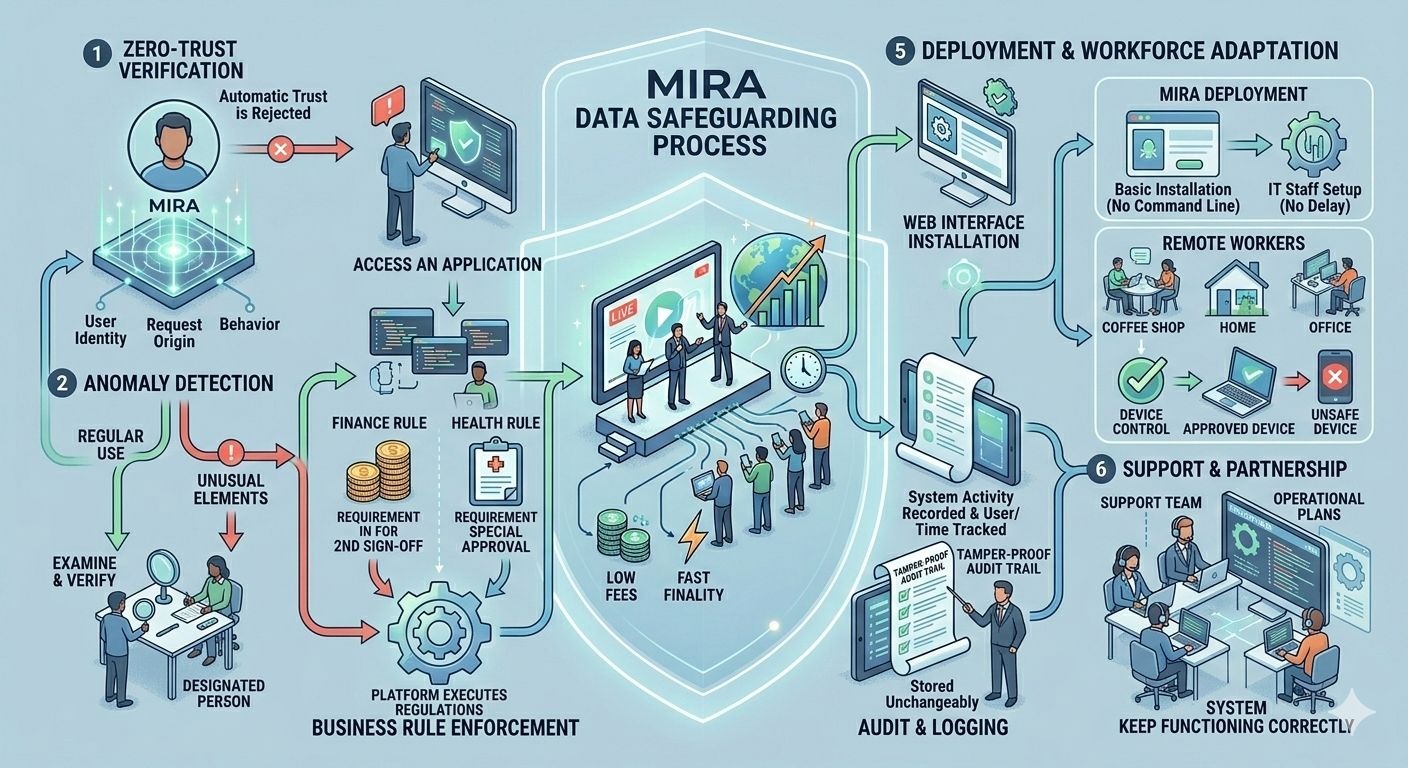
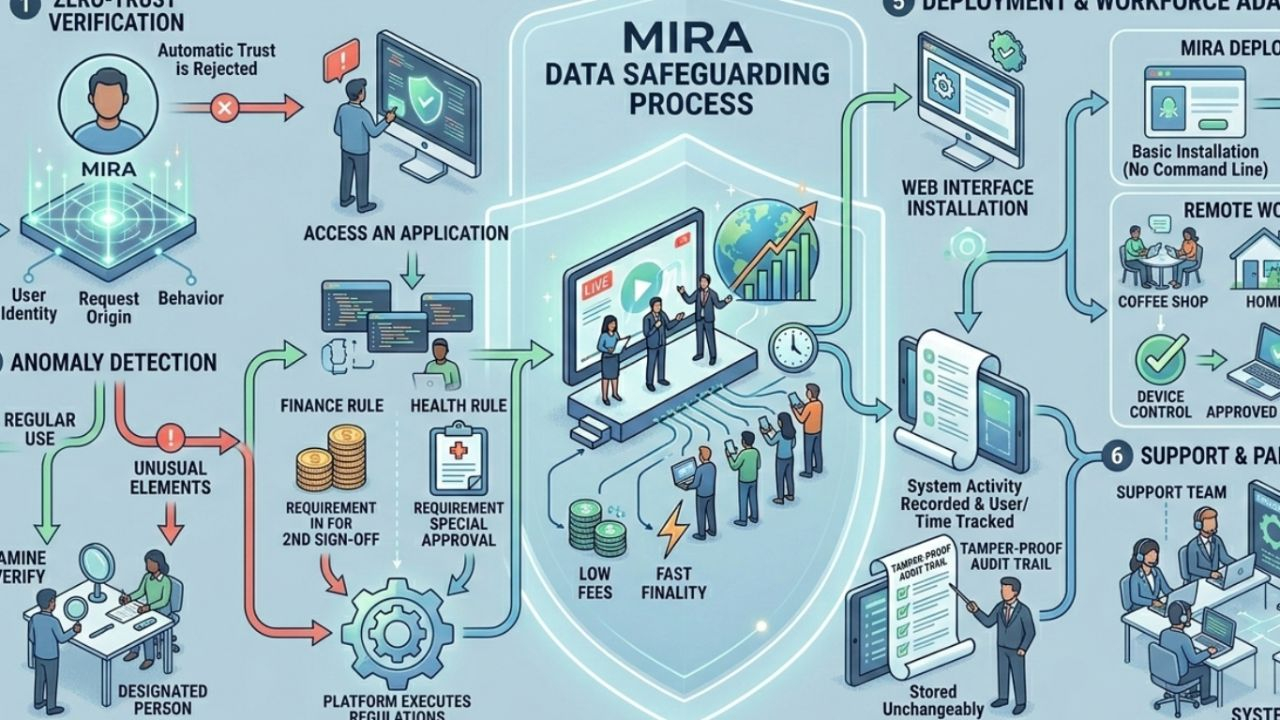
@Mira - Trust Layer of AI gives companies a way to keep their data safe while they use modern tools. The system operates on the principle that automatic trust should not exist throughout its operations because each request needs to undergo verification before access is granted. This idea can be used by any type of business from finance to health. The system protects all internal applications and all external partner connections.
The approach requires users to proceed through an initial verification step when they request to perform any action. The system evaluates user identity together with request origin and request behavior against established usage patterns. The system holds requests which contain any unusual elements until a designated person can examine them. The process protects against multiple attacks while allowing regular business activities to progress without any interruptions.
Business operations need to follow specific rules which the organization establishes through straightforward language. A finance team may require a second sign off for any transfer that is above a set amount. A health team may require a special approval before a patient record is opened. The platform automatically executes all these regulations. The platform keeps a record of all system activities through user identification and time tracking. The records are stored in a way that cannot be changed. This system enables auditors to view all events which occurred and organizations to analyze their previous experiences.
Mira deployment does not require complete network system changes. The system works with both existing cloud platforms and all on-site server installations. The installation process uses a web interface which shows users each installation step they have to complete. Basic installation requires no command line scripts. IT staff can set up the system without any delay because they do not need extensive training.
Remote workers can use the solution effectively. Employees can connect from home a coffee shop or any other place and still be subject to the same checks as they would be in the office. The system adapts to the network that is used and to the device that is being used. The control system blocks access to all unsafe devices while it lets approved laptops keep functioning.
The system allows all network traffic to operate normally because it stops only the activities which appear to be malicious. Users notice little slowdown. The system operates more efficiently when users have full access because they can use all available tools. The platform provides dedicated customer support through its support team. The support team develops operational plans through log analysis based on changes in business requirements. The partnership ensures that the system keeps functioning correctly throughout its entire lifespan.
Mira provides organizations with a method to safeguard their data through processes which never accept automatic trust as valid. The system verifies every request into the system while it documents all system activities through the creation of business rules which match operational requirements. The system now provides protection against security breaches while it enables rapid incident handling and maintains efficient operations for all users. Organizations which follow this model can direct their energy toward business expansion while they eliminate ongoing security management needs. The article is now prepared for publication on the designated publishing platform.
@Mira - Trust Layer of AI #Mira $MIRA