$MIRA Every developer building on AI infrastructure eventually hits "the moment." The API returns a 200 OK, the payload is clean, and your frontend renders a confident block of text. Everything looks perfect.
But here’s the kicker: The actual verification hasn't even finished yet.
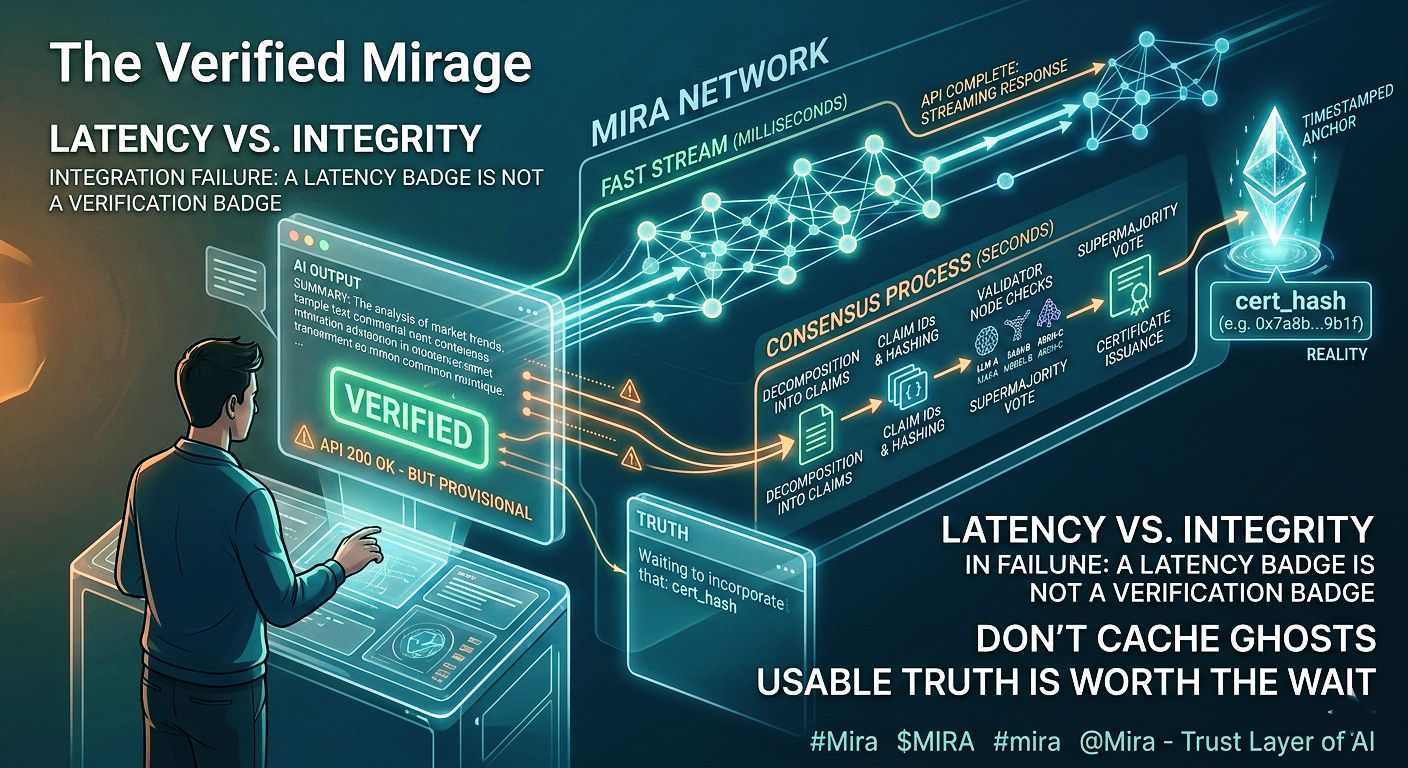
This isn't just a niche edge case; it’s a massive architectural tension. We’re trying to marry real-time user experience (which lives in milliseconds) with distributed consensus (which lives in rounds). When we prioritize speed over finalization, we end up with something dangerous: a "Verified" badge sitting on an output that hasn't actually been vetted.The Mira Network highlights this perfectly because its verification is truly distributed. When a query hits Mira, it doesn’t just get a quick rubber stamp. The output is broken down into claims, assigned IDs, and hashed. Validator nodes across the mesh run independent checks using different models and architectures.

A cryptographic certificate (the cert_hash) only gets issued once a supermajority agrees. That hash is the only thing that makes "verified" mean anything. It’s what auditors track and what gives the claim any real weight.
Without that hash, "green" is just a color on a screen.
The developer mistake is predictable:
Stream the response immediately so the UI feels snappy.
Let the certificate layer catch up in the background.
Treat the API success as verification success because, hey, the delay is only two seconds, right?
Wrong. Users don’t wait two seconds. They copy-paste, they send it to colleagues, and they make decisions based on that text instantly. By the time the certificate actually arrives, the unverified text is already out in the wild. You can’t claw it back.If you have a 60-second cache keyed to API success, you’re playing with fire. If a second request triggers a slightly different probabilistic response, you suddenly have two different "provisional" outputs circulating. Neither has a cert_hash. When things go wrong, support can’t even reconstruct what happened because the logs eventually show "Verified" once the certificate finally lands.
Everyone looks like they’re telling the truth, but nobody has a timestamped anchor to prove what the user actually saw.
This isn’t a flaw in Mira’s design—it’s an integration failure. Mira sells consensus-anchored truth, not just fast text. The cert_hash is the product. Everything before it is just a work-in-progress.
If your "Verified" badge triggers on API completion rather than certificate presence, it’s not a verification badge. It’s a latency badge. It tells you the server is awake, but it says zero about whether the output survived the gauntlet of validatorsGate the UI: Don't show "Verified" until the certificate is actually there.
Stop Caching Ghosts: Never cache provisional, uncertified outputs.
Display the Hash: Surface the cert_hash so downstream systems have something real to anchor to.
We have to accept that responsiveness is a UX value, but verification is an integrity value. Sometimes, they clash. When they do, you have to decide what your badge actually stands for.
Being "checkable" isn't the goal. Usable truth is. And usable truth is worth the two-second wait.