I think the easiest way to understand Sign Protocol is to stop treating public private and hybrid records as three separate ideas because they are really three ways of handling the same thing, which is a signed record built from a schema that other people or systems may need to verify later. Sign Protocol’s basic model feels fairly plain once I strip away the crypto language because a schema defines what kind of fact is being recorded and the format it should follow, while an attestation is the signed claim that fits that schema. From there the real question becomes less about whether something is onchain or offchain and more about who needs to see it and what still needs to remain provable over time, and I find that framing useful because it turns the topic from a technical branding exercise into a record keeping problem. Sign’s own docs now describe the protocol as an evidence layer that can be queried verified and audited across identity payment and distribution systems, which makes it feel less like a niche app and more like shared infrastructure for structured trust.
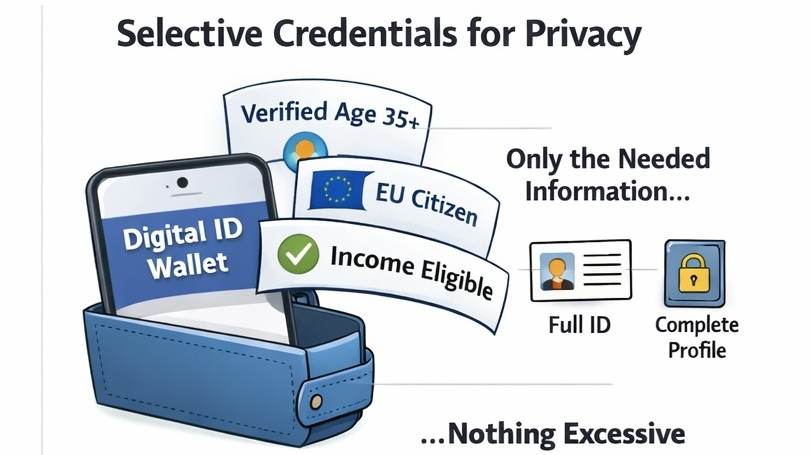
When I look at public records through that lens they make the most sense for facts that benefit from broad visibility because Sign describes public mode as transparency first, with wide accessibility and governance expressed through the chain or contract rules. That fits public eligibility proofs execution records and audit references where the point is that many different parties can inspect the same evidence on their own terms. Private records sit at the opposite end of that spectrum, although the docs are careful not to treat privacy as simple secrecy and I think that distinction matters because the goal is not merely to hide data but to let a system prove enough without exposing everything. The newer documentation talks about selective disclosure privacy preserving proofs private attestations and ZK based modes where they make sense, so the design is really about controlled visibility rather than absence. I used to think private systems like this mostly meant storing information somewhere else and asking people to trust the operator, but Sign’s framing is more specific because private mode is meant for confidentiality first environments, especially regulated ones, where permissioning membership controls and audit access policy decide who can inspect what and under what conditions.
Hybrid records are where the design starts to feel practical rather than ideological because Sign’s docs describe hybrid attestations as standard onchain attestations whose actual payload lives somewhere else such as Arweave or IPFS, while the onchain record keeps the metadata the schema link and an encoded content identifier that points to the external data. What stands out to me is how ordinary that logic feels once it is explained clearly, since if a record is too large to store cheaply onchain or too sensitive to expose in full it makes sense to keep the heavier or more delicate part offchain while leaving an onchain anchor that can still be checked later. That is not really a compromise in the sloppy sense but a division of roles between the part that must stay globally legible and the part that only needs to be retrievable inspectable or disclosed under the right conditions. The builder docs also present Sign Protocol as supporting fully onchain records fully Arweave records and hybrid records, which makes the whole system feel less like it is pushing one correct answer and more like it is acknowledging that records live under different cost privacy and access constraints.
I think that is one reason this subject is getting more attention now than it would have five years ago because the pressure is no longer just to prove that something happened on a blockchain. The harder problem now is proving that a person asset payment or compliance check can be verified across messy real world systems without leaking more information than necessary, and Sign’s current docs are full of identity money and capital use cases with repeated emphasis on audit trails eligibility evidence privacy preserving verification and regulated deployments. Outside Sign’s own material the broader conversation has also shifted in the same direction because recent writing on compliance attestations argues that tokenized assets and regulated onchain activity need verifiable proofs of offchain facts while also needing privacy controls strong enough for institutional use. So when Sign Protocol talks about public private and hybrid records I do not hear three fashionable labels but an attempt to answer a harder question about how records can stay inspectable portable and useful without forcing every fact into the same visibility model, and that does not remove the uncertainty because hybrid systems still depend on retrieval layers private systems still depend on access rules and interoperability still carries trust assumptions, yet that honesty is part of what makes the model easier for me to take seriously.
@SignOfficial #SignDigitalSovereignInfra $SIGN