I find it helpful to start with what I thought this kind of system was supposed to do. I used to think privacy and accountability pulled in opposite directions and that any framework promising both was probably hiding the tradeoff somewhere in the fine print. The more I look at the Sign framework the more I think its real point is simpler than that because it tries to separate three questions that often get mashed together: what should stay private what authority someone actually has and what can later be proven about what happened.
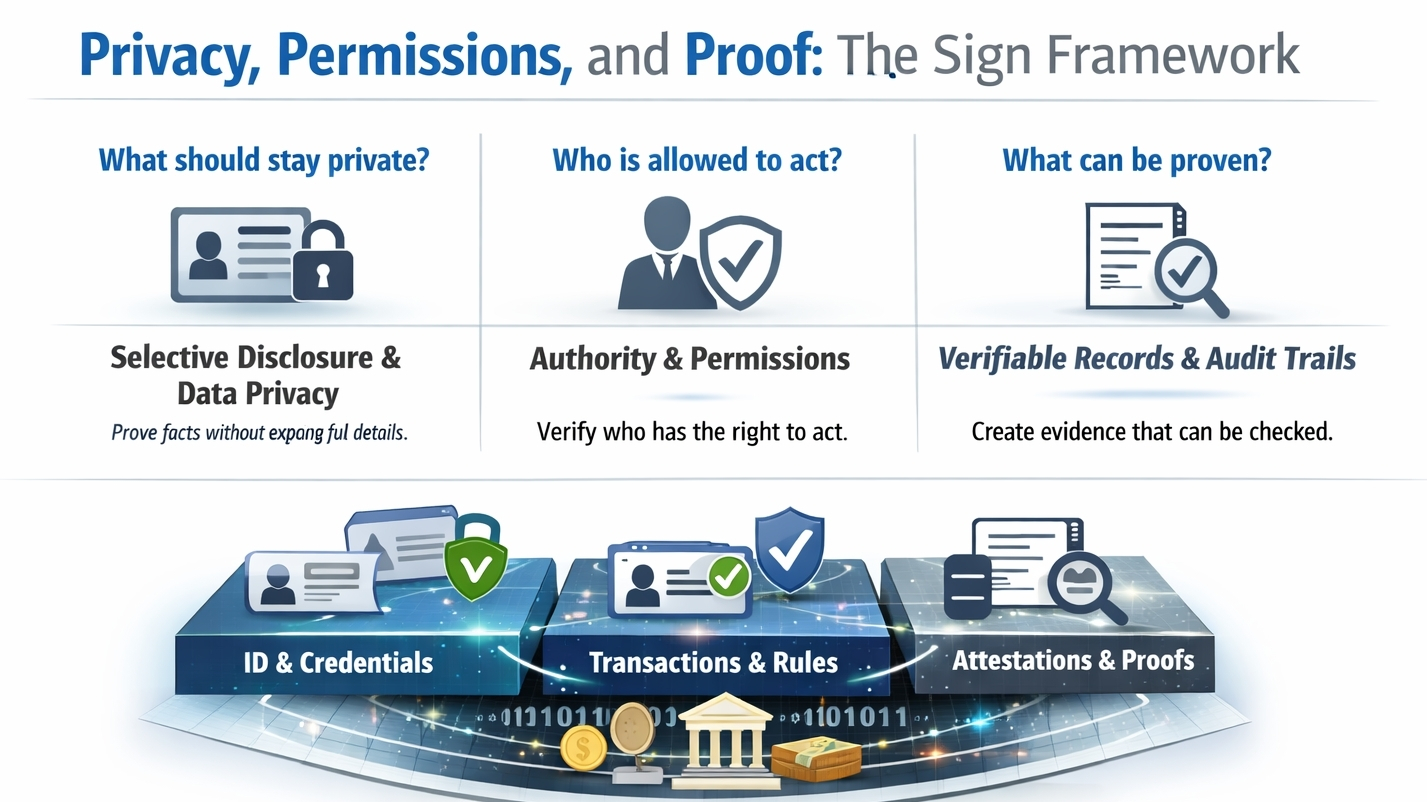
What makes this framework interesting to me is that it does not begin with a single app or a single chain. In Sign’s own description S.I.G.N. is a broader architecture for digital systems around money identity and capital while Sign Protocol works as the evidence layer inside that architecture. That distinction matters because it shifts attention away from the wallet the database or the payment rail and puts it on the claim itself. A person is eligible. An institution is authorized. A payment was executed. A rule was applied. Those claims are then turned into structured attestations that can be verified later instead of being left as loose entries scattered across disconnected systems.
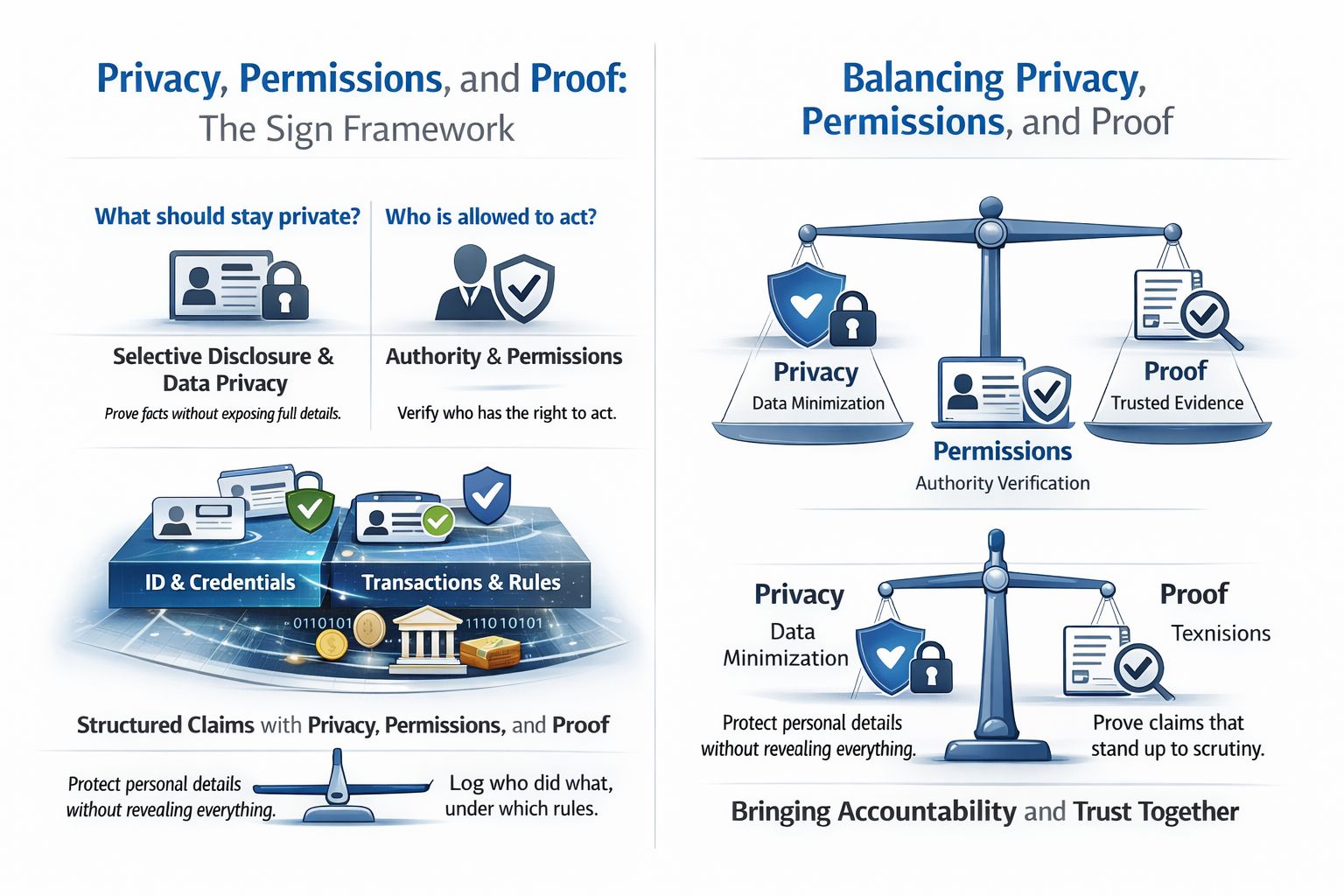
Privacy in that setup is not treated as silence which I think is the first thing people miss. It is treated as controlled disclosure. The framework leans on ideas like selective disclosure public and private attestation modes and zero knowledge proofs so that someone can prove a fact without dumping all the underlying data into view. In the Sign materials that can mean proving an attribute such as age or nationality without exposing the whole identity record. In the European digital identity wallet work the same logic shows up very clearly because users are meant to share only what is needed while protections against tracking and profiling are built into the design. That feels like a big reason this topic is getting more serious attention now because the technology is being framed less as a clever cryptography exercise and more as a practical way to enforce data minimization.
Permissions are the part I think sounds dull until something goes wrong because most systems are good at asking whether a person is signed in and much worse at asking whether that person agency or service is actually allowed to issue a credential approve a payment revoke a record or act on someone else’s behalf. Sign’s documentation keeps returning to authority verification role based permissions policy controlled delegation and logged governance actions. I read that as an effort to make permission a first class object instead of an afterthought buried in admin settings. In other words the real question is not only who you are but what authority you had under which rules and at which moment.
Then there is proof which is really where the framework earns its name. An attestation is the signed statement but the supporting evidence can include documents cryptographic proofs verification records or audit artifacts. Verification is not just checking a signature because it also means checking the schema the issuer’s authority and the status of the record including revocation or expiration. I like that this avoids the usual fantasy that digital truth is permanent and frictionless and instead admits that records can age permissions can change and mistakes need correction. In the Sign model the usual answer is not to erase history but to append a revocation a superseding attestation or a dispute record. That feels like a more realistic idea of trust because it is not perfect memory but inspectable memory.
What surprises me is how much of this lines up with broader movement outside Sign itself. W3C finalized Verifiable Credentials 2.0 in 2025 and NIST also finalized a new revision of its digital identity guidance in that same year. So the energy around frameworks like this is not coming from nowhere. The question has shifted over time because five years ago much of the conversation was about whether digital credentials were even real enough to matter while now the pressure is on interoperability revocation privacy and proof that can survive contact with regulators auditors and ordinary users.
I still think the hard part is governance rather than math because a framework can make it possible to prove only what is necessary but someone still has to decide what is necessary. A system can log permissions cleanly but someone still defines the roles. A proof can be valid while the surrounding policy is still unfair or overreaching. That uncertainty does not make the model useless. To me it makes the model honest. The Sign framework is most persuasive when I stop reading it as a promise to solve trust once and for all and start reading it as a disciplined way to keep privacy permissions and proof from collapsing into one vague word: trust.
@SignOfficial #SignDigitalSovereignInfra $SIGN