@MidnightNetwork #night $NIGHT

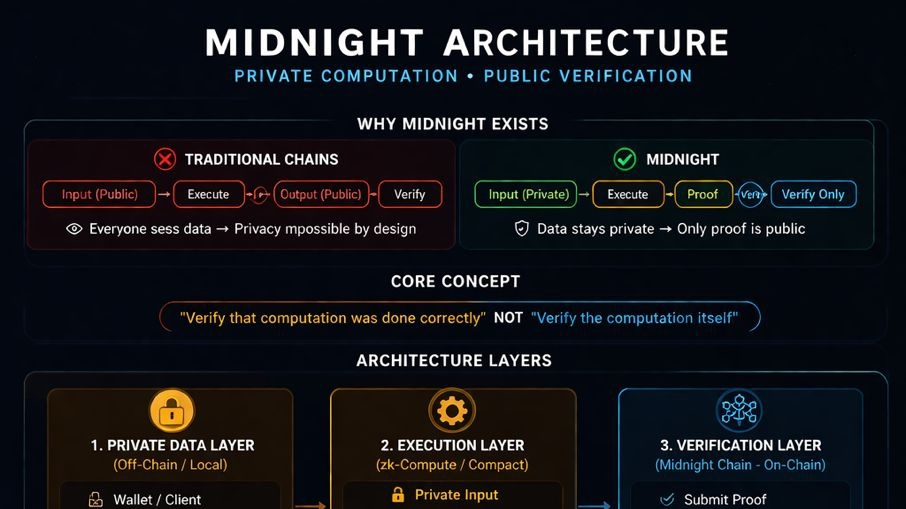
Most chains are built around one assumption:
Every node needs to see the data to verify the result.
That’s why everything becomes public.
It’s not a design choice. It’s how verification works in those systems.
Midnight changes that assumption.
Not by hiding data but by changing what the chain actually verifies.
Instead of verifying raw inputs and outputs, Midnight verifies a proof that computation was done correctly.
That changes the workflow completely.
Normal chain:
user sends data → contract executes → data + result visible → validators check everything
Midnight flow:
user keeps data private → computation happens → proof is generated → chain verifies proof only
The chain never touches the underlying data.
Now look at what’s happening inside that.
There are three separate parts:
1. private data layer User inputs never need to be broadcast publicly
2. execution layer Logic runs, but not in a way that leaks inputs
3. verification layer (on chain) Only the proof is checked, not the data
This separation is the core of Midnight.
Most chains combine all three.
Midnight splits them.
That’s why privacy is not a feature here. It’s part of the execution model.
Now bring in Compact.
Instead of writing contracts that assume public state, developers define:
what needs to be proven
not what needs to be shown
So a contract doesn’t say:
“store this data and execute it”
It says:
given some hidden input, prove this condition is true
That’s a different way of thinking.
Now real usage starts to make sense.
Identity:
User doesn’t upload identity data anywhere They generate a proof that they meet a condition (age, access, credentials)
System verifies the proof Nothing else is exposed
Payments:
Transaction details don’t need to be visible Amounts, relationships, flows can stay private
What the chain checks:
Was the transaction valid? Was it authorized?
Not:
Who paid who, how much, and why
Compliance:
This is where it gets practical.
Instead of sharing full records, a system can prove:

rules were followed
without exposing internal data
That’s something current chains can’t do cleanly.
The important part is this:
Midnight doesn’t try to hide data after execution.
It avoids exposing it in the first place.
Verification happens without requiring visibility.
That’s why it feels different from privacy add ons.
It’s not:
public system + privacy layer
It’s:
private computation + public verification
If you look at it this way, Midnight is less about transactions.
and more about proving that something happened correctly without revealing how.
That’s the part most people miss.
And that’s where its real use starts.