@Pixels #pixel $PIXEL I’ve spent enough time in crypto to know how easy it is to fall in love with narratives that sound structurally important. Over the years I’ve watched entire sectorsDeFi primitives, gaming economies, and identity frameworksrise on the strength of convincing arguments about inevitability. Yet many of them struggled to move beyond discussion and speculation. The gap between an idea that feels necessary and a system people actually rely on daily is much wider than the market usually admits. That skepticism has shaped how I look at projects like Pixels, not just as a game, but as a behavioral environment where identity, ownership, and economic activity intersect in ways that reveal how infrastructure really behaves under repeated use.
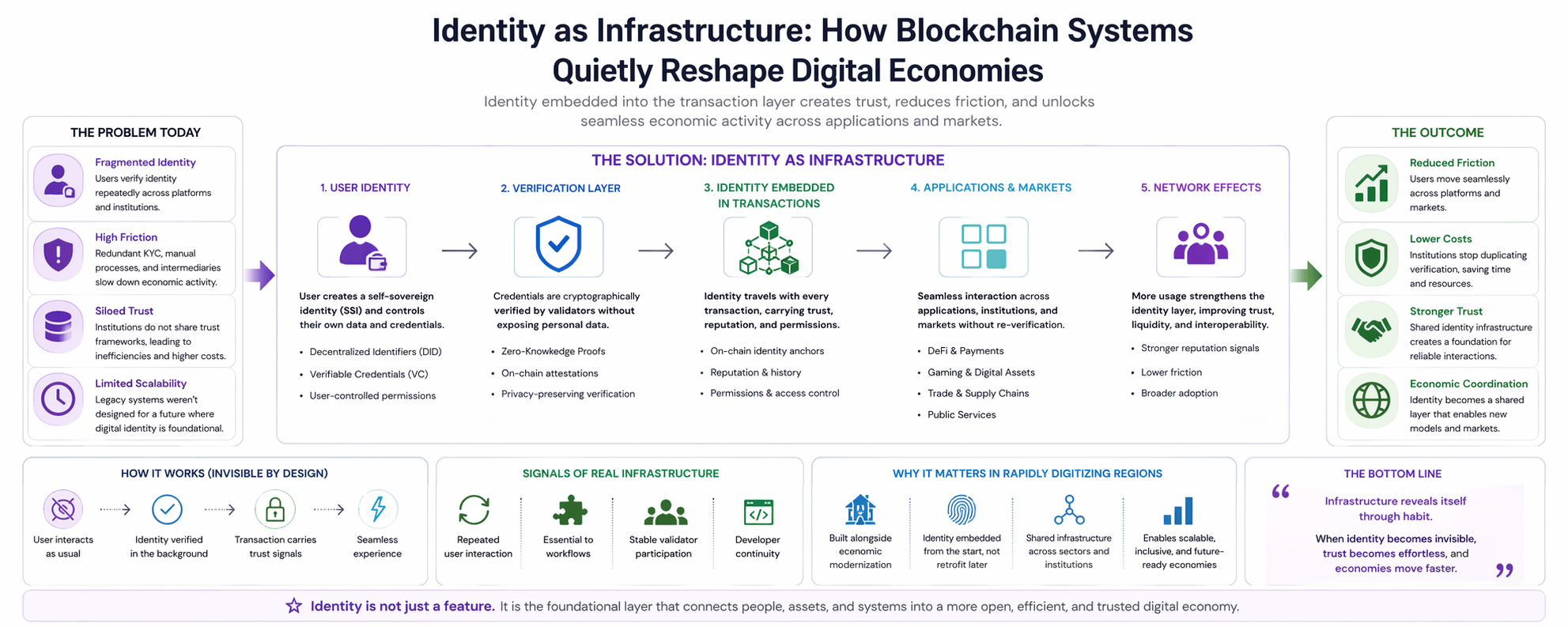
What interests me less about blockchain gaming is the entertainment layer and more about the systems quietly operating underneath. In environments like Pixels, identity isn’t simply a login credentialit becomes an operational layer tied to assets, reputation, and transaction history. When identity is embedded directly into financial interactions rather than sitting above them, the architecture of trust changes. Instead of relying on centralized verification or intermediaries to validate every action, the system itself begins to accumulate context about participants. That context, when designed properly, reduces friction across markets because participants don’t have to repeatedly prove who they are or what they’ve done.
But this only works when identity infrastructure is designed to remain almost invisible. The best implementations I’ve interacted with are the ones users barely notice. Identity verification happens quietly in the background, cryptographic attestations confirm legitimacy, and the transaction layer carries the necessary signals without forcing users through constant checkpoints. When systems get this balance wrongwhen verification becomes overly intrusivethe user experience shifts dramatically. People hesitate, transactions slow down, and trust erodes not because security failed but because the interaction itself feels hostile.
Repeated interaction exposes these design flaws quickly. I often notice it in subtle moments: a pause before confirming a transaction, a second attempt after a delayed response, or a user abandoning a workflow altogether. Systems reveal their real character in these micro-behaviors. Identity infrastructure that feels seamless fades into the background; identity infrastructure that demands attention becomes friction.
This behavioral dynamic becomes even more interesting when viewed through the lens of rapidly digitizing regions such as the Middle East. In many of these economies, digital infrastructure is being built alongside economic modernization rather than layered on top of decades of legacy systems. That creates a rare design opportunity. Financial rails, trade platforms, and public digital services can be constructed with identity embedded from the beginning rather than retrofitted later.
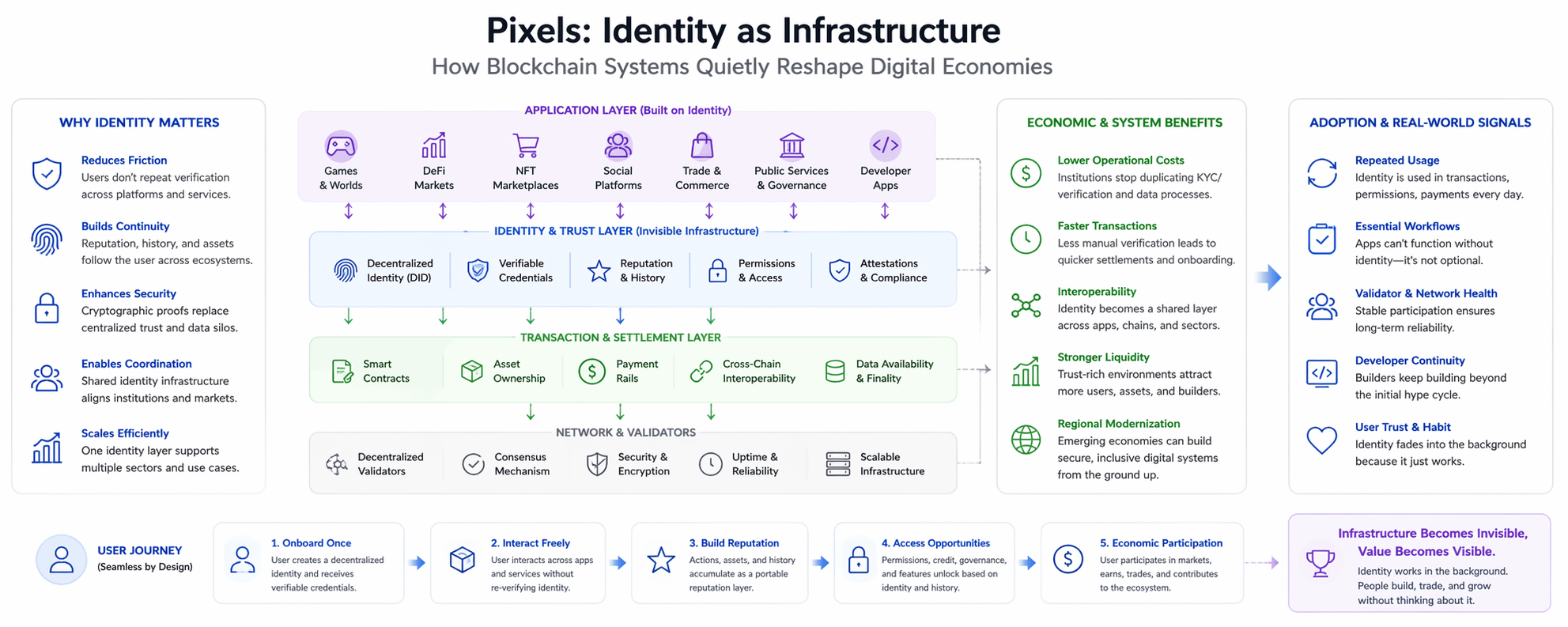
Separating identity from financial systems has historically created inefficienciesduplicated verification processes, fragmented trust frameworks, and institutions that spend enormous resources validating the same information repeatedly. Integrating identity directly into transaction infrastructure could gradually reduce those inefficiencies. The interesting part isn’t theoretical efficiency gains; it’s how coordination across sectors might evolve when identity becomes a shared layer across markets, institutions, and applications.
Still, the market often gets ahead of reality. I see trading activity surge around identity-focused blockchain narratives long before meaningful usage appears. Attention, liquidity, and token speculation tend to reflect expectations rather than observable adoption. It’s a familiar pattern: investors respond to the structural importance of the idea, while the underlying systems are still searching for consistent workflows where identity actually matters.
That distinction becomes obvious when you watch how frequently users interact with the identity layer itself. Real infrastructure reveals itself through repetition. If identity is truly embedded in economic activity, users will rely on it constantlyoften without realizing it. Transactions, permissions, and reputational signals will flow through the same identity framework every day. If instead identity only appears during onboarding or occasional verification events, then it remains more of a conceptual layer than operational infrastructure.
When I evaluate systems like this, I look for signals that extend beyond narrative strength. Are users interacting with identity-linked systems repeatedly? Are there applications where identity is essential rather than optional? Is validator or network participation stable enough to support long-term infrastructure? Are developers continuing to build once the initial excitement fades?
These signals matter because infrastructure rarely announces itself dramatically. It becomes visible through habit. The difference between an idea that sounds necessary and a system that becomes necessary is simple: people rely on it repeatedly, often without thinking about it at all. In my experience, that quiet dependencynot narrative momentumis the clearest sign that a piece of blockchain infrastructure is beginning to matter.