When I started learning more about Midnight Network, one thing quickly became clear. The goal is not simply to hide information. The real focus is building a privacy layer that can still work with regulated environments.
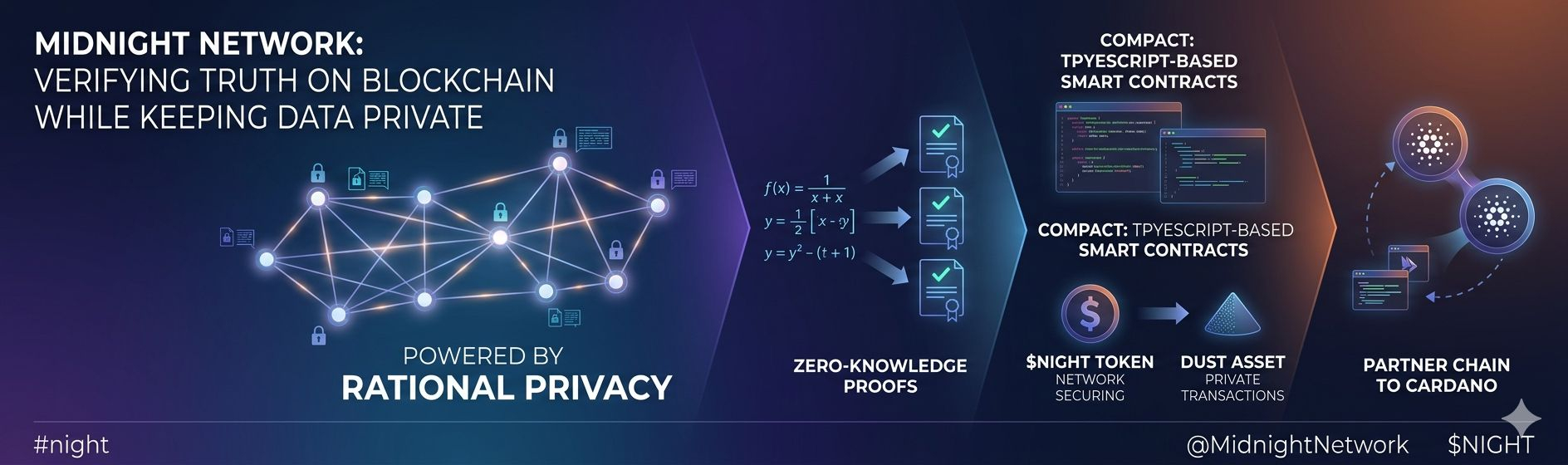
Many privacy focused blockchains try to hide everything. Midnight takes a different approach. The network uses what it calls rational privacy. This means applications only reveal the information that regulators, businesses, or partners actually need. Everything else can stay private.
Another interesting part is how Midnight connects with the Cardano ecosystem. It is not designed as a completely separate privacy chain. Instead it works as a partner chain connected to Cardano. Because of this design Midnight can benefit from Cardano liquidity, infrastructure, and validator network while focusing on privacy based applications.
In my opinion this approach is very smart. Midnight is not trying to compete with other blockchains. Instead it adds a new capability that allows the ecosystem to do more.
The technical structure is also interesting. Midnight separates the system into two layers. The public blockchain handles consensus, settlement, and governance. The private environment runs the smart contract logic where sensitive data is processed. Only a zero knowledge proof is shared with the public ledger to confirm that the computation was correct.
This means the blockchain never sees the private data itself. It only verifies that the rules were followed.
Midnight is also trying to make privacy application development easier. The network introduces Compact, a smart contract language built with TypeScript. Privacy cryptography can often be complex for developers, but Compact allows them to clearly define which parts of an application remain private and which parts are public.
In other words, privacy becomes something developers can program directly into their applications instead of relying only on the blockchain itself.
The economic model of Midnight follows this separation as well. The token NIGHT is used for securing the network and participating in governance. Another asset called DUST is derived from NIGHT and is used for private transactions inside the system.
This structure separates network ownership from the resources used to power private activity.

