Blockchain was built on the promise of transparency. Every transaction can be verified by anyone, which removes the need for central authorities. This model works well for trustless finance, but it introduces a growing problem. When everything is transparent, privacy begins to disappear. Wallet histories become traceable. User behavior can be analyzed. In some cases, sensitive financial activity becomes visible to the entire internet.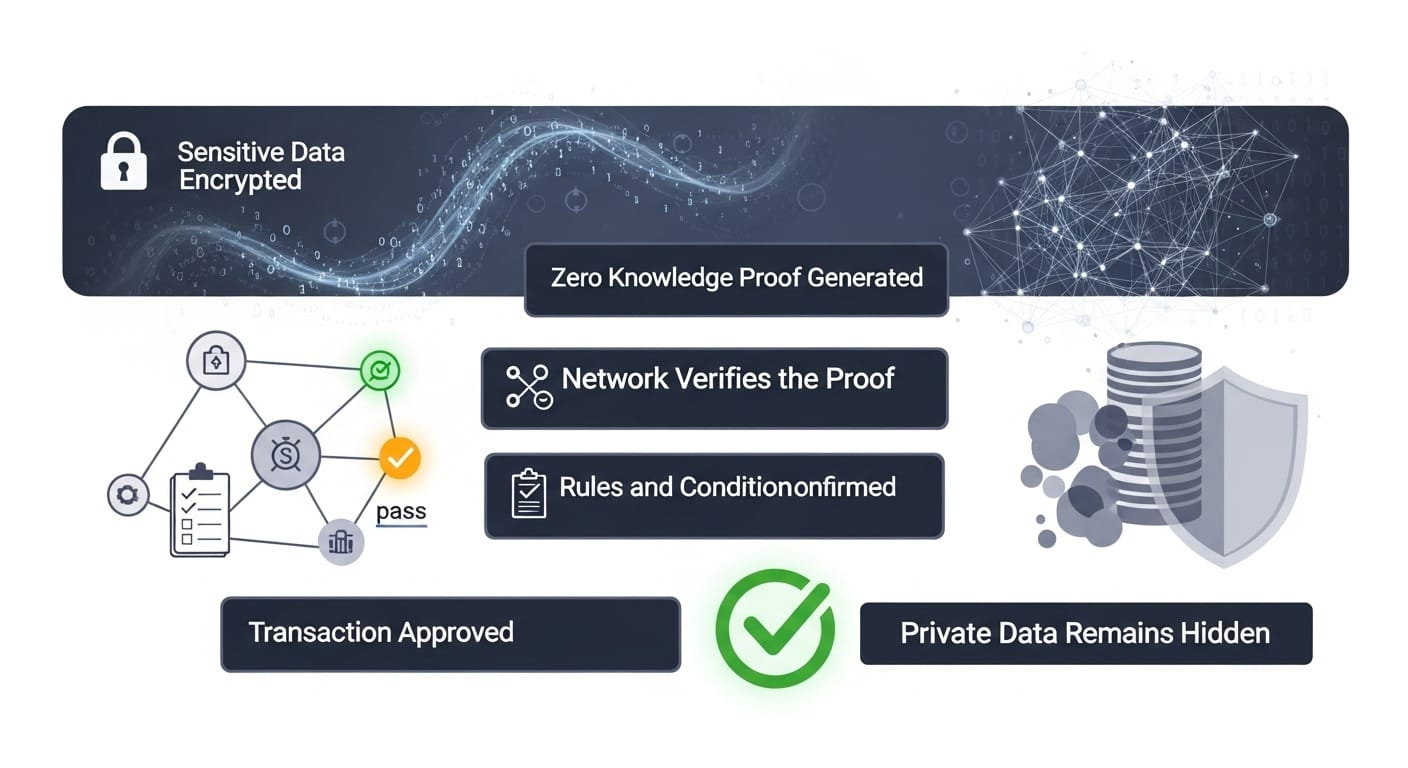
This tension between transparency and privacy is now one of the most important debates in the crypto industry. The next generation of blockchain infrastructure is trying to solve this problem without sacrificing the core principle of verification. One project exploring this direction is Midnight Network, which uses advanced zero knowledge cryptography to confirm transactions without exposing the underlying data.
To understand the concept, imagine entering a building that requires age verification. In the traditional system, you would show your passport or identification card. The guard would see your name, your address, your photo, and other personal details. However, the only information the guard actually needs is confirmation that you are above a certain age. Everything else is unnecessary exposure.
Zero knowledge verification works in a similar way. Instead of revealing the entire identity document, the system only proves the specific condition required. The verifier receives confirmation without accessing the sensitive information itself. This is the core idea behind the privacy architecture being explored by Midnight Network.
In blockchain systems, this concept becomes extremely powerful. A transaction can be verified as valid without exposing wallet balances, user identities, or internal application data. The network can confirm that rules are followed while sensitive information remains protected.
This shift is important because the blockchain industry is entering a new phase of development. In the early days, most users were crypto enthusiasts experimenting with decentralized finance. Today the ecosystem is expanding toward enterprise platforms, digital identity systems, and real world financial infrastructure. These sectors require both transparency and privacy at the same time.
Financial institutions, for example, must comply with regulations that require auditability. At the same time they are obligated to protect client data. Healthcare applications must verify medical credentials without revealing patient information. Supply chain systems must confirm transactions without exposing proprietary logistics data.
Without privacy preserving infrastructure, many of these use cases cannot safely operate on public blockchains.
This is where zero knowledge systems become a strategic innovation. They allow networks to maintain cryptographic trust while preventing unnecessary data exposure. The verification remains decentralized, but the personal information stays confidential.
From a market perspective, privacy technologies are becoming one of the strongest narratives in the blockchain sector. Over the last few years the industry focused heavily on scalability, modular architecture, and layer two networks. Those improvements increased transaction speed and reduced costs. The next challenge is protecting the data flowing through these networks.
Projects building privacy layers are essentially solving the next bottleneck in blockchain adoption. If scalable infrastructure allows millions of transactions per second, privacy infrastructure determines whether those transactions can safely involve real world users and institutions.
In my personal view, the importance of zero knowledge verification is still underestimated by the market. Many investors focus on visible metrics like transaction volume or token price movement. Infrastructure innovations tend to gain recognition slowly because their value becomes clear only after developers begin building applications on top of them.
But historically, the most important shifts in crypto have come from infrastructure upgrades. The introduction of smart contracts changed what blockchains could do. Layer two networks changed how they scale. Privacy verification could change how people interact with decentralized systems entirely.
At this stage of the article, a useful visual could illustrate how zero knowledge verification works.
Chart suggestion one
User submits transaction
Sensitive data remains encrypted
Cryptographic proof generated
Network verifies proof
Transaction approved without exposing private data
This diagram helps readers visualize the difference between verification and disclosure.
The opportunity created by privacy infrastructure extends across multiple sectors. Decentralized identity systems could allow individuals to prove qualifications without revealing full identity details. Voting systems could confirm eligibility while keeping ballots confidential. Financial applications could process transactions without exposing personal account data.
For developers, the ability to build applications that protect user data opens an entirely new design space. Instead of forcing users to reveal everything to the network, applications can request only the minimum proof required for each interaction.
However, this innovation is not without challenges. Zero knowledge cryptography is complex and computationally intensive. Building efficient systems requires advanced engineering and continuous optimization. If transaction verification becomes too expensive or slow, adoption may suffer.
Regulatory perception is another factor. Some policymakers may initially misunderstand privacy technologies and associate them with illicit activity. In reality, the goal of privacy infrastructure is the opposite. It allows legitimate users and businesses to operate securely without exposing sensitive information to public surveillance.
The success of projects working on privacy solutions will therefore depend on both technical performance and responsible ecosystem governance.
Another visual that could strengthen this article would focus on real world applications.
Chart suggestion two
Digital identity verification without revealing personal data
Enterprise supply chain tracking with confidential information protection
Financial transactions verified without exposing balances
Healthcare records confirmed without sharing patient details
This chart shows how zero knowledge systems expand the range of blockchain use cases.
Looking ahead, the long term direction of blockchain technology appears to be evolving toward selective transparency. Instead of publishing every detail to a public ledger, networks will verify correctness while controlling which information becomes visible.
This approach mirrors how the internet itself evolved. Early internet protocols lacked encryption, which meant sensitive data could be exposed during communication. Over time secure layers like encrypted connections became standard. Today users expect privacy as a default feature.
Blockchain infrastructure may be approaching a similar transition. Verification will remain decentralized, but exposure will become optional rather than mandatory.
For investors and developers watching the evolution of privacy technology, the direction explored by Midnight Network highlights an important shift in how trust is built within decentralized systems.
Instead of forcing users to reveal everything to prove they are legitimate, the network can confirm truth without demanding full disclosure. It is essentially the blockchain equivalent of proving you meet the requirement without handing over your passport.
If this model becomes widely adopted, it could unlock an entire generation of decentralized applications that combine transparency, compliance, and privacy in ways that earlier blockchains could never achieve.
@MidnightNetwork #night $NIGHT

