 A while back I noticed a pattern in how blockchain discussions usually unfold. Someone introduces a new protocol, and the conversation quickly turns toward performance numbers. Transaction speed, block time, throughput, scalability. Those metrics matter, but they often dominate the conversation so much that another question quietly disappears.
A while back I noticed a pattern in how blockchain discussions usually unfold. Someone introduces a new protocol, and the conversation quickly turns toward performance numbers. Transaction speed, block time, throughput, scalability. Those metrics matter, but they often dominate the conversation so much that another question quietly disappears.
What kind of information should a blockchain actually store?
That question is where Midnight Network starts to feel different.
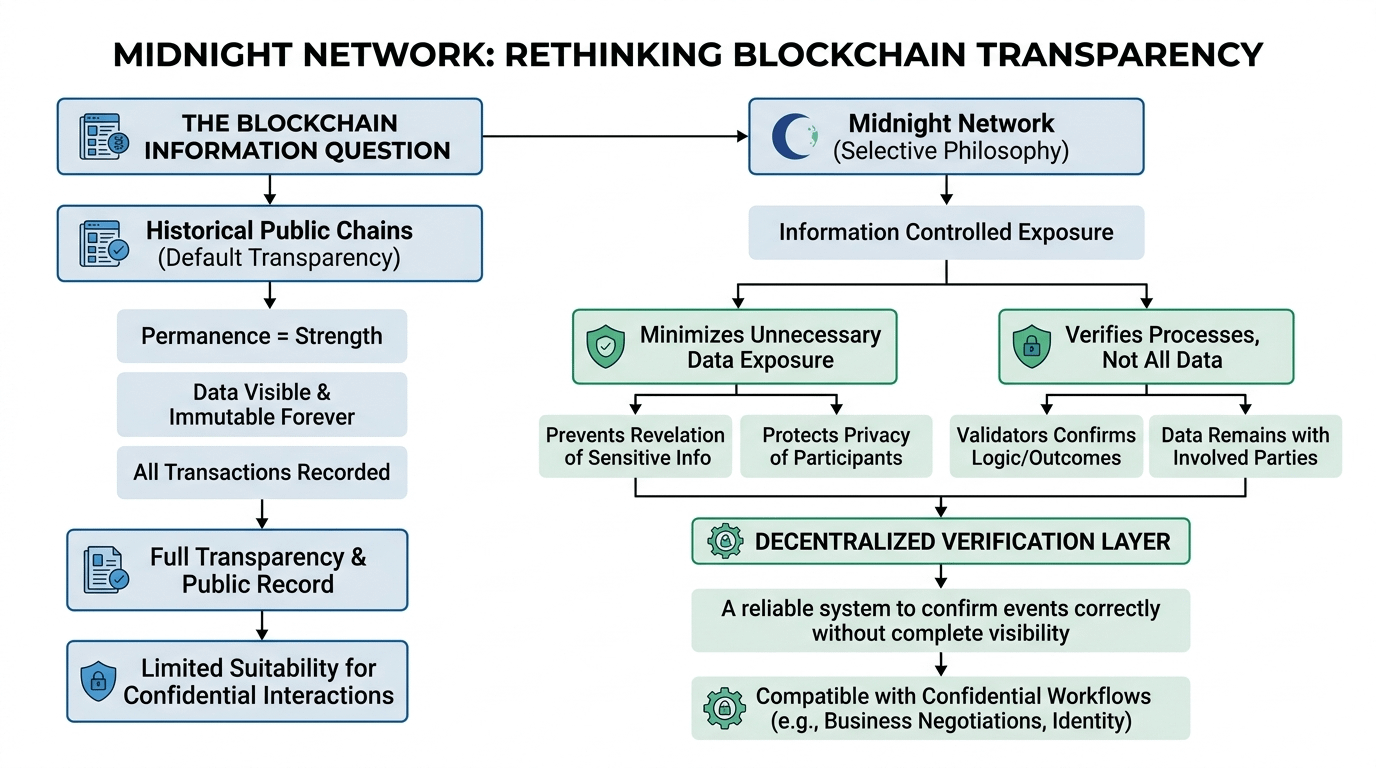
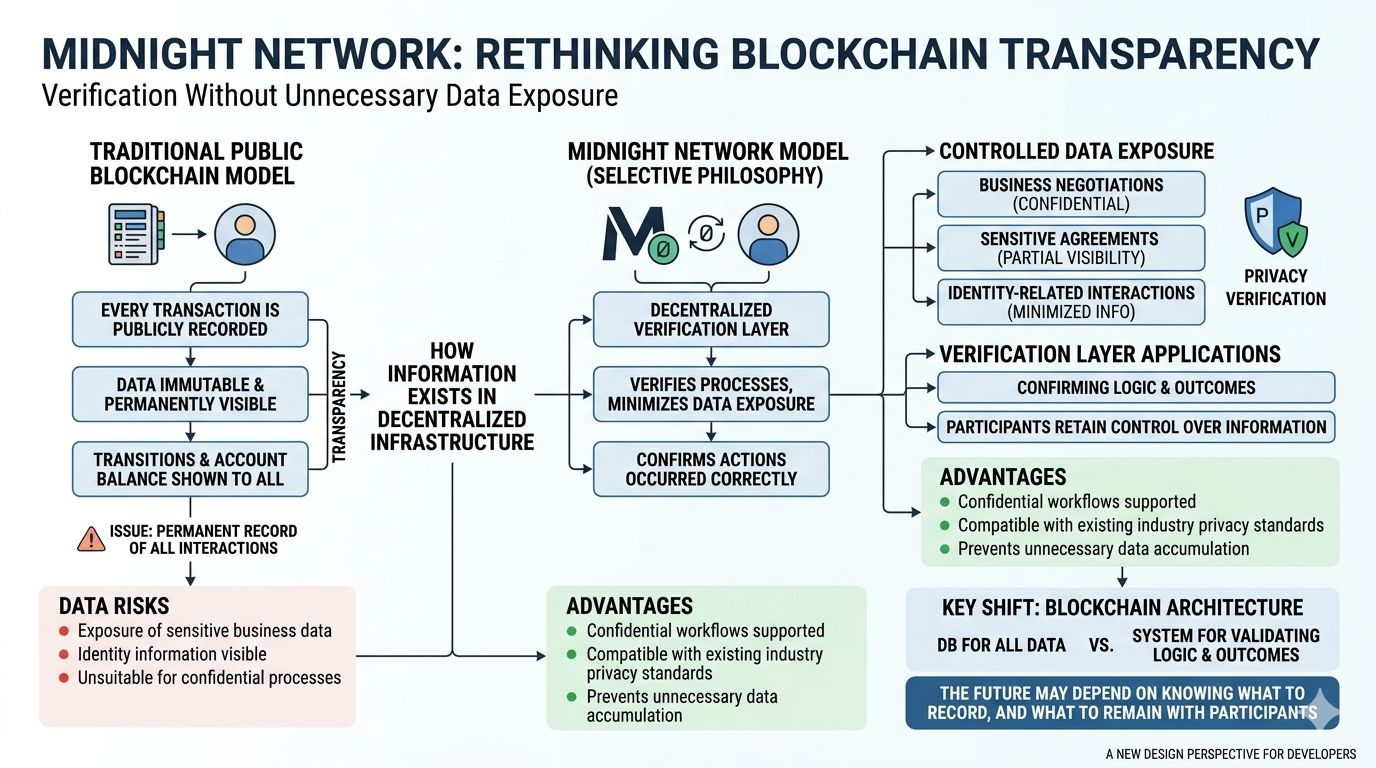
Instead of focusing only on how quickly data can move through a system, Midnight appears to be examining how information itself should exist inside decentralized infrastructure. Public chains historically treat data permanence as a strength. Once something enters the ledger, it remains visible and immutable forever. That design supports transparency, but it also creates a permanent record that may not always be appropriate for every type of interaction.
Midnight seems to be built around a more selective philosophy.
Rather than assuming every interaction must become permanent public history, the network explores how decentralized systems can verify processes while minimizing unnecessary data exposure. The goal is not to remove accountability from blockchain environments, but to prevent systems from collecting or revealing information that does not need to be publicly stored.
That distinction can change how developers think about blockchain architecture.
Many real-world processes involve information that cannot be broadcast openly. Business negotiations, sensitive agreements, or identity-related interactions often require confidentiality while still needing a reliable system to confirm that events occurred correctly. Midnight’s design suggests that decentralized verification does not always require complete public visibility.
For developers, this introduces a new design perspective.
Instead of treating blockchain like a public database where everything must be recorded, applications can treat the network as a verification layer that confirms actions without exposing the entire context behind them. The protocol becomes a system for validating logic and outcomes while allowing participants to keep control over the information surrounding those interactions.
That model could make blockchain infrastructure feel more compatible with everyday systems.
Organizations that rely on confidential workflows often avoid fully transparent networks because they cannot expose internal processes. If Midnight’s approach proves practical, it could allow decentralized verification to exist alongside the privacy expectations that many industries already operate under.
Still, architecture alone does not guarantee adoption.
The real measure of Midnight’s direction will appear as developers begin experimenting with what the network makes possible. When builders start designing applications that rely on controlled information exposure rather than default transparency, the system’s philosophy will begin to show its value.
Because in the long run, the future of decentralized technology may not depend on recording everything.
It may depend on knowing exactly what should be recorded and what should remain in the hands of the people involved.