1. Context: Privacy and Structural Problems in Crypto
Many blockchain systems promise transparency, security, and decentralization. Yet those same traits create a major tension. Public ledgers expose transaction data, which can undermine privacy and commercial confidentiality. Over the past decade, projects such as and attempted to solve this through privacy techniques, while platforms like focused on programmable smart contracts.
The project known as aims to combine programmable infrastructure with zero knowledge cryptography. It is closely connected to the ecosystem surrounding and the research driven company .
Its core claim is simple. It wants to allow applications to run with strong privacy while still maintaining accountability, regulatory compatibility, and data ownership. In theory this would allow businesses and individuals to interact on chain without exposing sensitive information.
The question is not whether the idea sounds appealing. The real question is whether the design actually solves structural problems in crypto networks, or if it simply repackages familiar ideas under new language.
2. Does Midnight Solve Structural Problems or Reframe Old Ideas?
Zero knowledge proofs are not new. They have existed in cryptography research for decades and entered the blockchain world through systems like Zcash. What Midnight proposes is not merely using zero knowledge for payments but integrating it deeply into a programmable network.
The structural problem it claims to solve is this: public blockchains reveal too much information, while private systems sacrifice decentralization.
Midnight attempts to create a hybrid structure where computation and verification happen on chain, while sensitive data remains hidden.
This is conceptually elegant. Yet the challenge lies in whether the architecture actually addresses the limitations seen in earlier systems.
Past privacy networks faced three major issues:
First, heavy computational costs.
Second, limited developer adoption.
Third, regulatory concerns about complete anonymity.
Midnight attempts to address all three simultaneously. It uses zero knowledge circuits to protect data, while allowing selective disclosure and compliance mechanisms.
However, one must ask whether this is genuinely new architecture or simply a layered version of ideas already explored in other networks. Many modern blockchains are already experimenting with privacy layers, rollups, and off chain computation.
In that sense Midnight may represent evolutionary development rather than a structural breakthrough.
3. Separating Token Roles: Design Improvement or Added Complexity?
A distinctive feature of Midnight is the separation of token functions. The ecosystem introduces different assets with different responsibilities.
One token handles governance and value capture. Another resource unit powers transactions and computation.
In theory, separating economic roles avoids conflicts between speculation and network usage. It also attempts to stabilize transaction costs by decoupling them from token price volatility.
This idea appears logical at first glance. Yet it introduces a deeper question about usability.
Crypto already struggles with complexity. Many users do not fully understand gas fees, staking, bridging, or liquidity pools.
Introducing multiple tokens can increase cognitive load for both users and developers.
For example:
A developer building an application must understand how both assets interact.
A user interacting with that application must hold the correct resource token to perform actions.
If this system is not carefully abstracted by wallets and applications, it could recreate the same friction that plagued early decentralized finance platforms.
From a pure design perspective the separation is rational. From a user experience perspective it may create additional layers that normal users never asked for.
4. Friction for Everyday Users
Most blockchain design discussions happen in theoretical environments. Engineers assume rational users who understand wallets, fees, and cryptographic proofs.
Real users behave very differently.
They forget passwords.
They misunderstand fees.
They abandon systems that require too many steps.
A protocol can be technically brilliant but still fail if interaction feels confusing.
Midnight introduces privacy preserving execution and complex resource models. These systems may require specialized development tools and wallet support.
If interacting with the network requires understanding batteries, privacy circuits, or token separation, then adoption could slow.
The critical factor will be whether these mechanisms remain invisible to the end user.
If the system allows applications to hide the complexity behind simple interfaces, friction may remain low.
If not, the protocol risks becoming a platform appreciated mainly by researchers rather than mainstream users.
5. The Battery Resource Model
One of the more unusual aspects of Midnight is its battery style resource model.
Instead of traditional transaction fees, users rely on a resource system that behaves somewhat like rechargeable capacity.
The idea attempts to solve a long standing blockchain problem. Transaction fees fluctuate wildly when network demand rises.
By introducing a predictable resource model, Midnight aims to create more stable interaction costs.
This design could have advantages:
Users may not need to calculate gas fees every time they perform an action.
Applications can estimate resource consumption more predictably.
Network congestion may be handled through resource limits rather than price spikes.
However, there are tradeoffs.
Users are already familiar with the concept of paying a fee. Replacing that with an abstract battery model might introduce new confusion.
People may ask questions such as:
Why is my battery empty?
How do I recharge it?
Why did this transaction drain more capacity than expected?
If these questions become common, the design could unintentionally increase user frustration rather than reduce it.
The success of this model depends heavily on wallet design and clear feedback.
6. Privacy Versus Accountability
Pure privacy systems often face criticism from regulators and institutions.
Completely anonymous networks raise concerns about money laundering, sanctions evasion, and illicit finance.
Midnight attempts to address this tension by supporting selective disclosure.
Users can prove certain facts about data without revealing the underlying information.
For example:
A user might prove they meet compliance requirements without revealing personal details.
This model attempts to balance confidentiality with accountability.
In theory this is one of the strongest aspects of the design. It allows organizations to build applications that protect sensitive data while still meeting legal obligations.
Yet there is a philosophical challenge.
Privacy advocates may view selective disclosure as compromising anonymity. Regulators may still distrust systems built on hidden data.
The protocol therefore sits in a middle ground that may satisfy neither extreme fully.
Whether this balance succeeds will depend less on cryptography and more on social acceptance.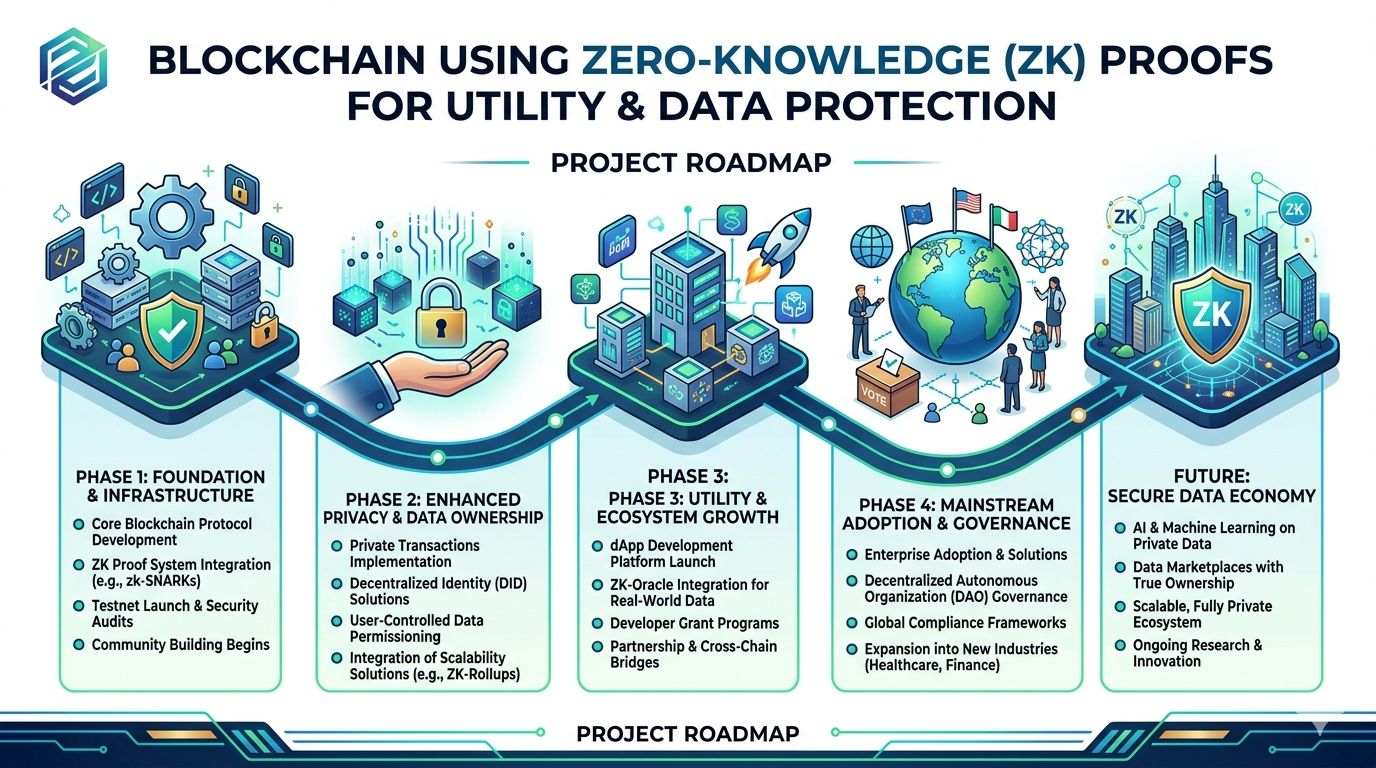
7. Market Patience for Complex Systems
Crypto markets historically reward simplicity and narrative clarity.
Many successful networks gained adoption because their value proposition was easy to understand.
Bitcoin offered digital scarcity.
Ethereum offered programmable contracts.
Midnight proposes a more sophisticated model involving privacy circuits, resource batteries, and token separation.
This raises an important question about market maturity.
Are users and developers ready for a platform that requires deeper conceptual understanding?
If the broader ecosystem matures, such complexity may be accepted as necessary infrastructure.
If speculative hype remains the dominant force, simpler narratives may continue to attract more attention and capital.
In other words, the technology might be ahead of the market's patience.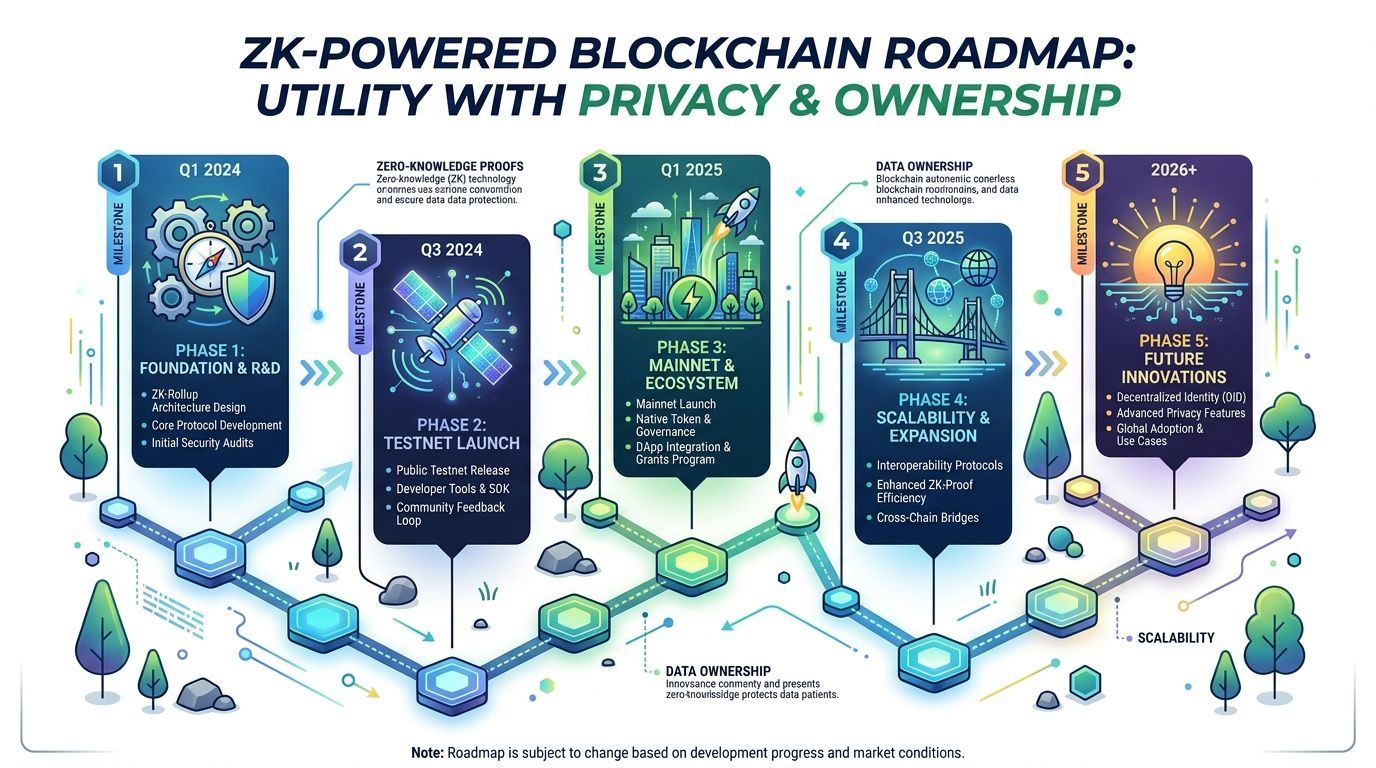
8. Technical Elegance Versus Real World Adoption
Many technically elegant systems fail not because they are flawed but because they struggle to build ecosystems.
Developer adoption depends on tools, documentation, and community.
If building on Midnight requires specialized cryptographic expertise, the number of developers capable of creating applications may remain limited.
By contrast, platforms like Ethereum succeeded partly because developers could learn the system quickly.
The challenge for Midnight is therefore not only technical design but developer accessibility.
If the tooling hides complexity and allows familiar programming models, adoption may grow steadily.
If development feels difficult, the network could remain academically impressive but practically underused.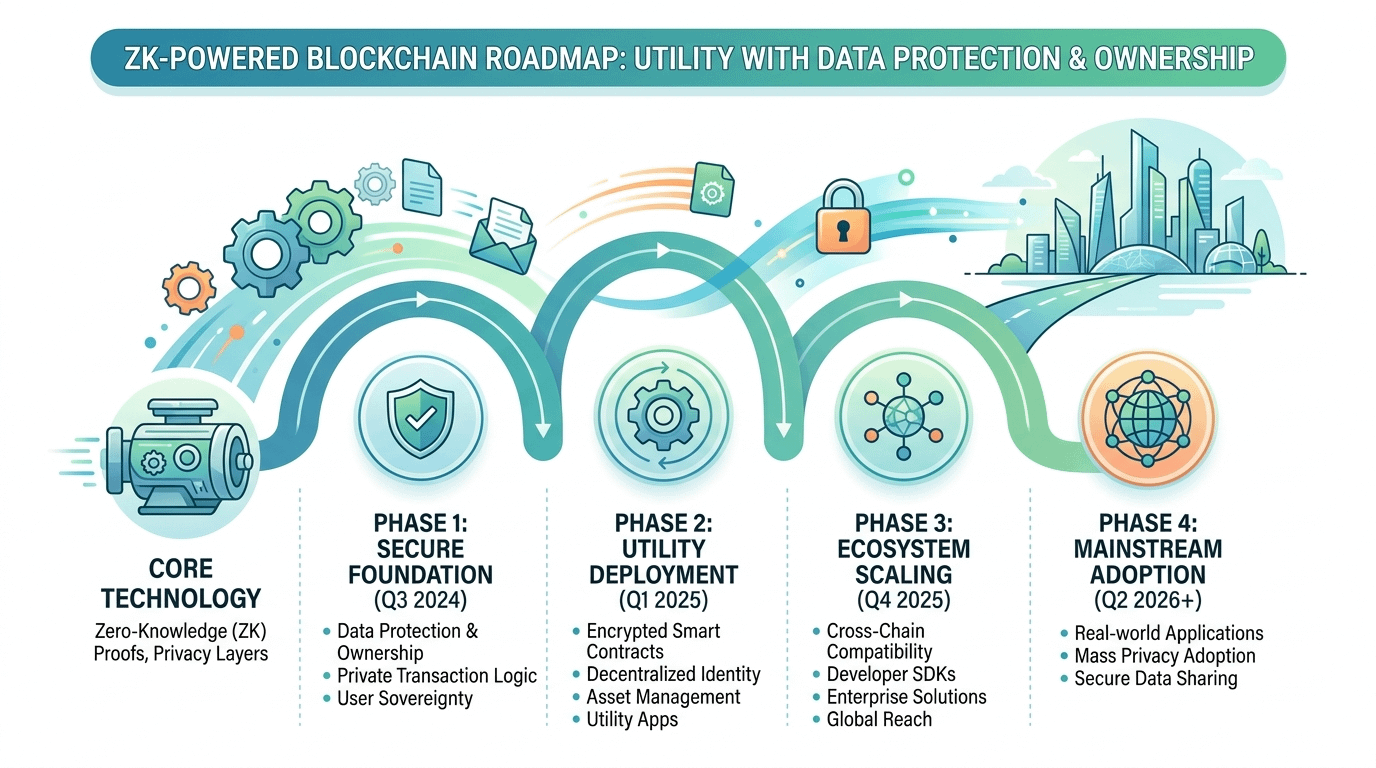
9. Failure Through Gradual Friction
Crypto failures often appear dramatic. Hacks, collapses, or regulatory crackdowns make headlines.
Yet many projects actually fade slowly.
They lose users gradually.
Developer activity declines.
Liquidity shifts elsewhere.
Midnight's biggest risk may not be catastrophic failure but slow erosion caused by friction.
Small inconveniences accumulate:
Wallet support arrives late.
Developers struggle with tooling.
Users misunderstand resource mechanics.
Each issue alone may seem minor. Together they can discourage participation.
Over time the ecosystem may stagnate even while the underlying technology remains sound.
This kind of failure rarely appears as a single moment. It looks more like quiet abandonment.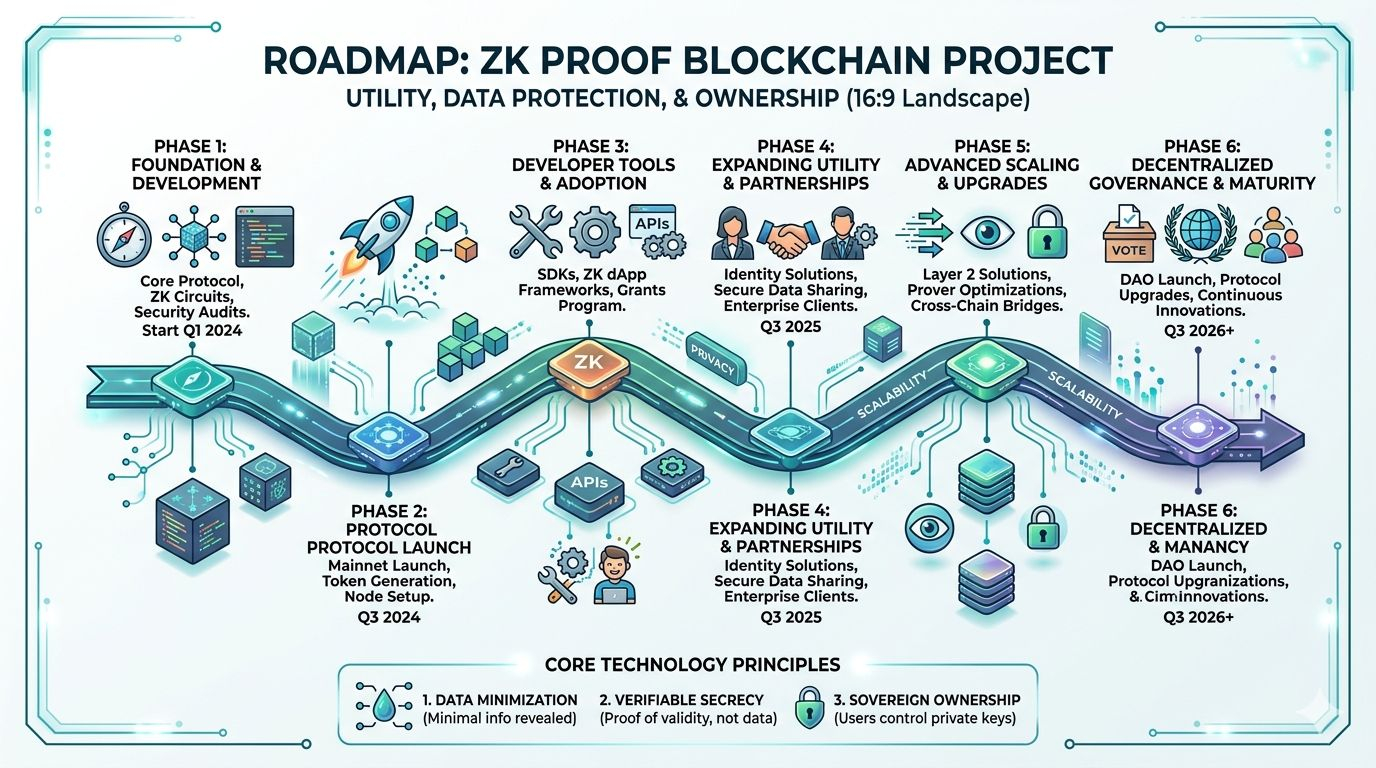
10. Genuine Design Vision or Crypto Narrative?
Finally, one must examine whether Midnight represents authentic engineering intent or simply a narrative aligned with current crypto trends.
Privacy, regulatory compatibility, and modular token economics are currently popular themes.
Projects often package these ideas into ambitious roadmaps that attract attention but deliver limited practical value.
Midnight appears different in one key respect.
The design originates from a research focused environment associated with Input Output Global and the academic culture around Cardano. This suggests genuine effort toward long term architecture rather than short term marketing.
However, even sincere design does not guarantee success.
Crypto history is filled with thoughtful systems that never reached meaningful scale.
Ultimately the difference between hype and lasting infrastructure lies in real usage.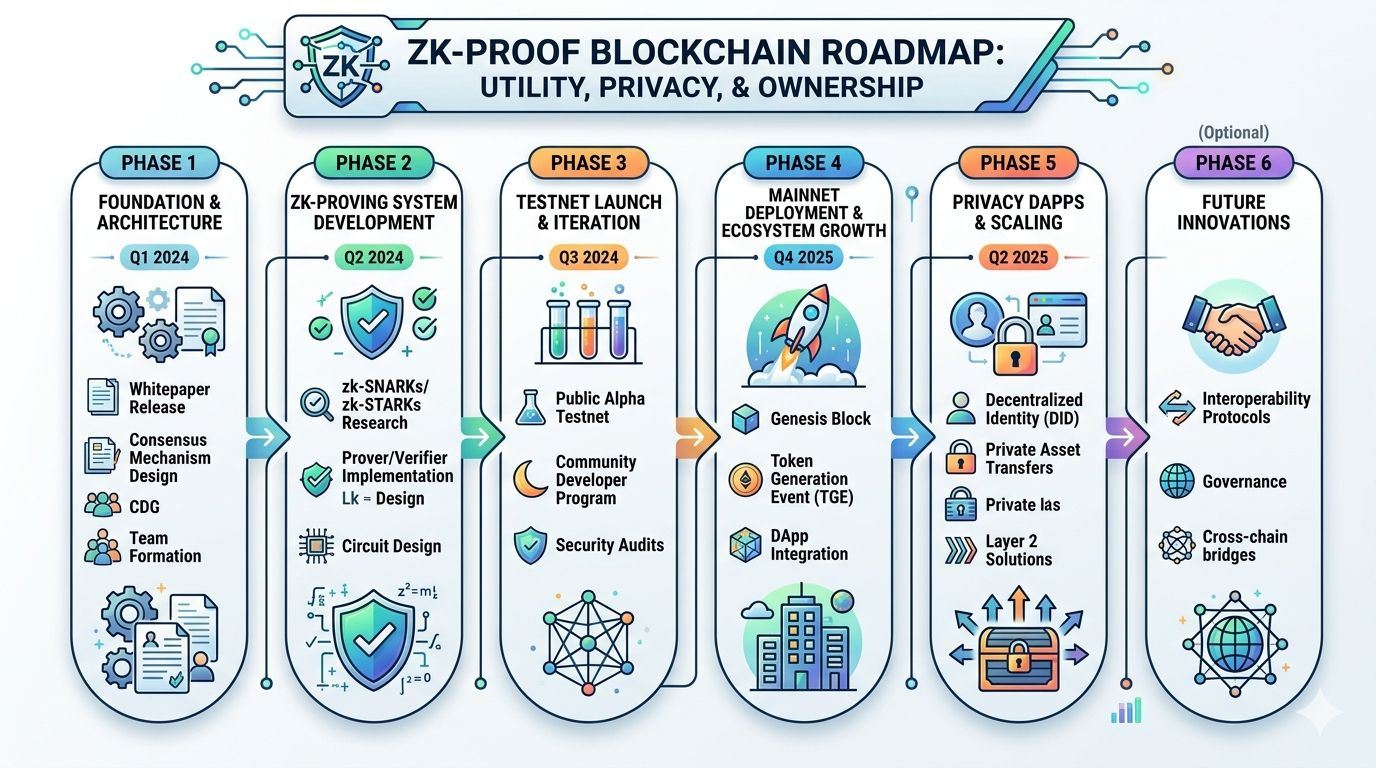
11. Final Assessment
Midnight Network represents an ambitious attempt to rethink privacy and usability in blockchain systems.
Its design introduces several interesting ideas:
zero knowledge based programmable privacy
separation of economic roles between tokens
a battery style resource model for predictable costs
selective disclosure mechanisms for regulatory compatibility
From a theoretical perspective these concepts address real weaknesses in existing networks.
Yet theory alone does not determine success.
The critical tests will occur in three areas:
user experience
developer adoption
ecosystem growth
If the protocol hides its complexity behind intuitive tools, it could become a powerful infrastructure layer for privacy preserving applications.
If complexity remains visible, the network may struggle to move beyond niche experimentation.
Midnight therefore sits at an interesting crossroads. It is neither pure hype nor guaranteed success.
It is a technically thoughtful system entering an environment where user behavior, market psychology, and developer incentives often matter more than elegant design.
Whether it thrives will depend on one simple measure.
Not whether the architecture works in theory, but whether ordinary users and developers actually choose to use it.

