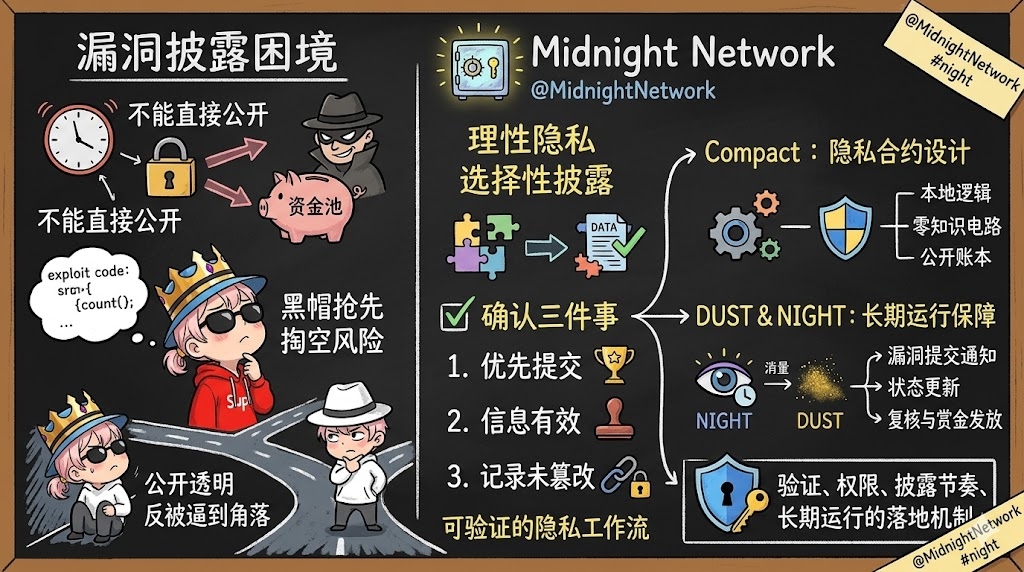
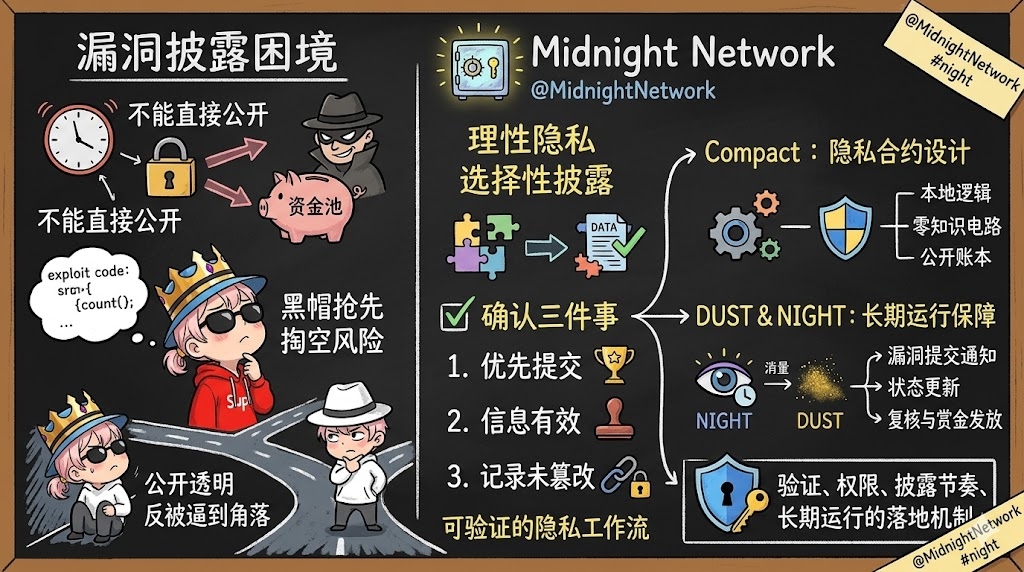
When a white hat discovers a contract vulnerability, the most dangerous moment is often not whether the code can be exploited, but the moment they are about to speak.
This situation on-chain is quite awkward. You need to notify the project party as soon as possible, otherwise the vulnerability may be discovered by someone else at any time.
But you can't just send the exploit path, key parameters, and reproduction methods directly to the public environment.
If the message is seen by black hats first, and the project party hasn't patched it, the funding pool may have already been emptied.
The most absurd situation is that the white hat wants to do the right thing, but is cornered by the very transparency of the matter.
In this scenario, it clearly showcases the core value of @MidnightNetwork .
@MidnightNetwork is not primarily about hiding everything, but about rational privacy.
To put it simply, it means proving what needs to be proven and not spreading what shouldn't be. The selective disclosure it has always emphasized fits particularly well into vulnerability disclosure.
What the project needs to confirm is not to first make the entire exploit public, but to first verify three things: whether this vulnerability was submitted by you first, whether this information is valid, and whether this record has been tampered with.
Locking down these three things first, and then disclosing the subsequent details at a steady pace, is what on-chain security processes should look like.
The role of Midnight is right here.
It does not simply provide you with a privacy box, but a verifiable privacy workflow.
You can first submit the vulnerability description, leaving a timestamp and proof of existence.
The project can confirm that the clues arrive first, the content is valid, and the submission order is clear, but outsiders cannot see the white hat identity or the complete exploitation details.
Wait until the patches are applied, the bounty rules are confirmed, and then decide how far to disclose.
This way, the on-chain retains verifiability, and the vulnerability information won't turn into a bomb for the whole network to watch due to premature exposure.
What underpins this is not an abstract concept.
Midnight's Compact was originally designed for this kind of privacy contract scenario.
Opening the ledger, zero-knowledge circuits, and handling local offline logic separately, what developers create is not a mess that only cryptography experts can understand, but a set of application logic that can truly run the process.
In scenarios like security bounties, anonymous reporting, and intelligence rewards, it solves not whether something can be hidden, but how to retain evidence while controlling the spread.
$NIGHT And the DUST set is not optional.
$NIGHT is the public native governance token and also a layer of capital.
DUST is generated by NIGHT, and what consumes DUST when executing transactions and contracts are the actions related to vulnerability submission notifications, status updates, follow-up reviews, and bounty disbursement. These actions are not one-time; the system needs to run long-term, and resources must be stable.
By doing this, the project does not have to calculate gas at every step, and developers can more easily turn these highly sensitive processes into long-term usable services.
So the core of Midnight is not just privacy.
Its real weight lies in merging verification, permissions, disclosure rhythm, and long-term operation into a set of implementable mechanisms.
In the process of vulnerability disclosure, the greatest fears are rush, collateral damage, and loss of control. What exactly is this project solving? It becomes clear at once.
@MidnightNetwork $NIGHT #night