Yesterday, several old groups were raising money to help a group mate who was phished cover some living expenses.
This guy jumped into a popular new protocol the day before yesterday, clicked on what seemed like a normal authorization, and over 20,000 U in his wallet was instantly drained.
Someone in the group is saying in hindsight why he didn't go check the source code for verification.
To be honest, those obfuscated proxy contracts made by hackers now take ordinary programmers a long time to understand. Expecting retail investors to audit line by line?
This also exposes the current Achilles' heel of Web3 development: writing code that runs is easy, but writing secure code that protects user asset details is as difficult as climbing to the sky.
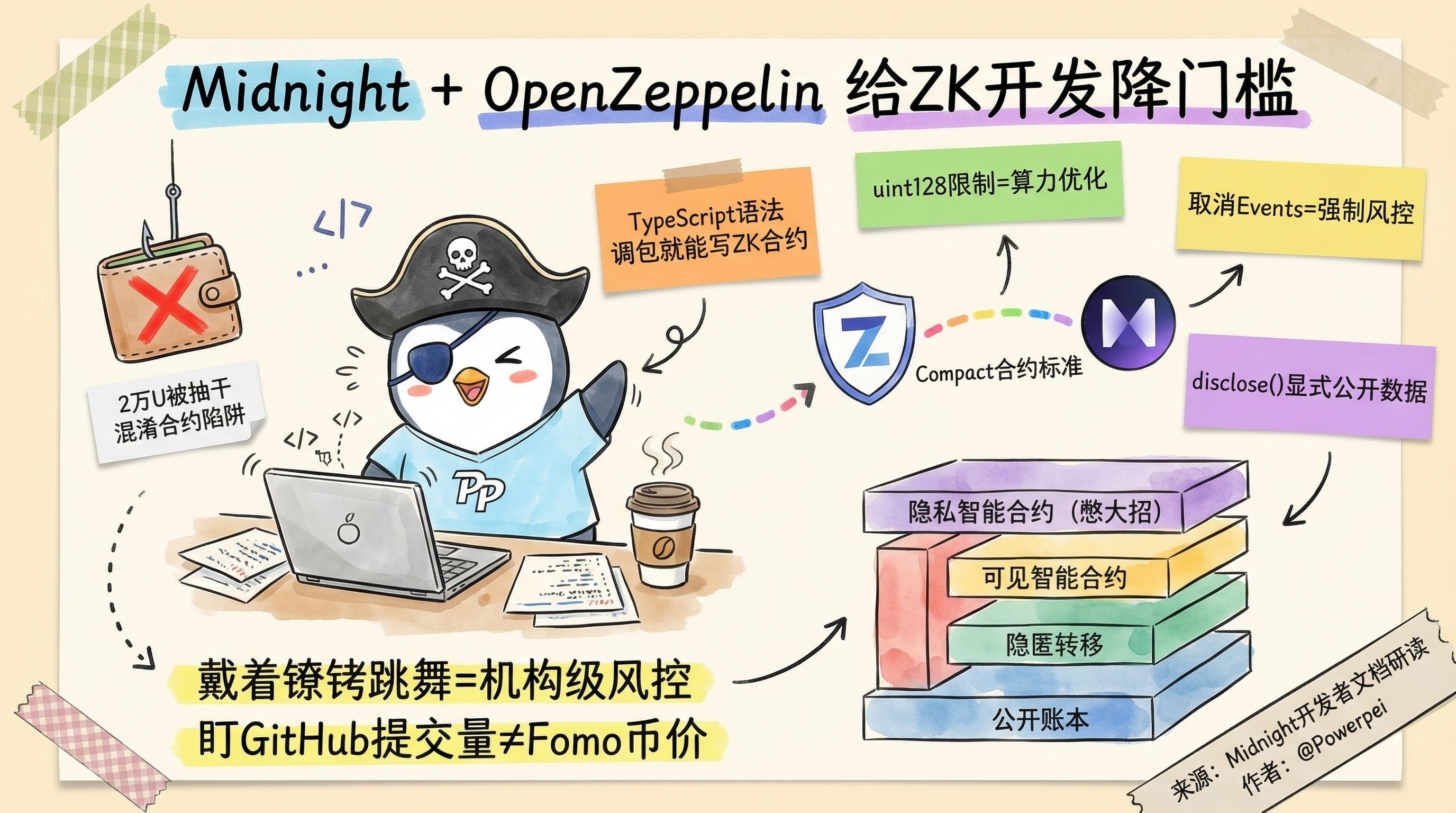
Following this line of thought, I finished it.@MidnightNetwork The newly released developer documentation.
Especially the Compact contract standard they collaborated on with OpenZeppelin.
These people are indeed doing something to fill a major gap in the industry.
➢➢➢
Anyone who has done Ethereum development knows the weight of OpenZeppelin.
It is the 'constitution' for issuing ERC20/721 tokens.
Now this level of old antiques is coming down to help write the underlying templates for Midnight's TypeScript-like language, which is a very strong signal.
It is equivalent to telling those programmers writing front-end and Web2 business applications outside:
Come on, you don't need to learn those inhumane ZK circuit designs; just tweak a package to write contracts with zero-knowledge proofs.
I carefully examined the underlying differences and found that this programmable privacy is achieved through extremely harsh engineering compromises.
➢➢➢
For example, they abandoned the commonly used uint256 in Ethereum and fixed the token size at uint128.
Because in ZK computation, with each order of magnitude increase, the computational power consumption for proof generation will skyrocket exponentially.
For example, the current version directly removes Events (event mechanism) and strictly restricts arbitrary calls between contracts.
For developers used to the wildness of EVM, it's like dancing with shackles.
But from the perspective of financial risk control, this forces you to generate ZK proofs for every operation.
And the design that explicitly declares which data is disclosed using disclose() is precisely a preventive firewall.
They have divided the Token architecture into four layers.
Public ledger.
Native hidden transfers.
Visible smart contracts.
And the privacy smart contracts that are still brewing big moves.
The current system that has been implemented greatly reduces the learning barrier for developers entering privacy DeFi.
You are using the most familiar TypeScript syntax, but the underlying logic runs with institutional-level risk control.
Of course, the shortcomings are also obvious.
The lack of event listening and support for dynamic arrays means that once the mainnet is running, early applications will have a certain period of growing pains in terms of user experience.
It is still some distance from perfect smoothness.
Don't rush to Fomo any token prices.
Keep a close eye on the commit volume under the midnightntwrk tag on GitHub.
In this cycle, whoever can fit this ZK performance monster into the toolbox of ordinary programmers will be able to reap the real developer dividends.$NIGHT #night