Aapka article already strong hai, lekin maine isey structure, clarity aur conviction ke level par aur tighten kiya hai repetition kam ki, arguments sharper kiye, aur ending ko aur powerful banaya hai. Yeh refined version hai:
SIGN and the Structural Convergence of Digital Identity and Token Distribution
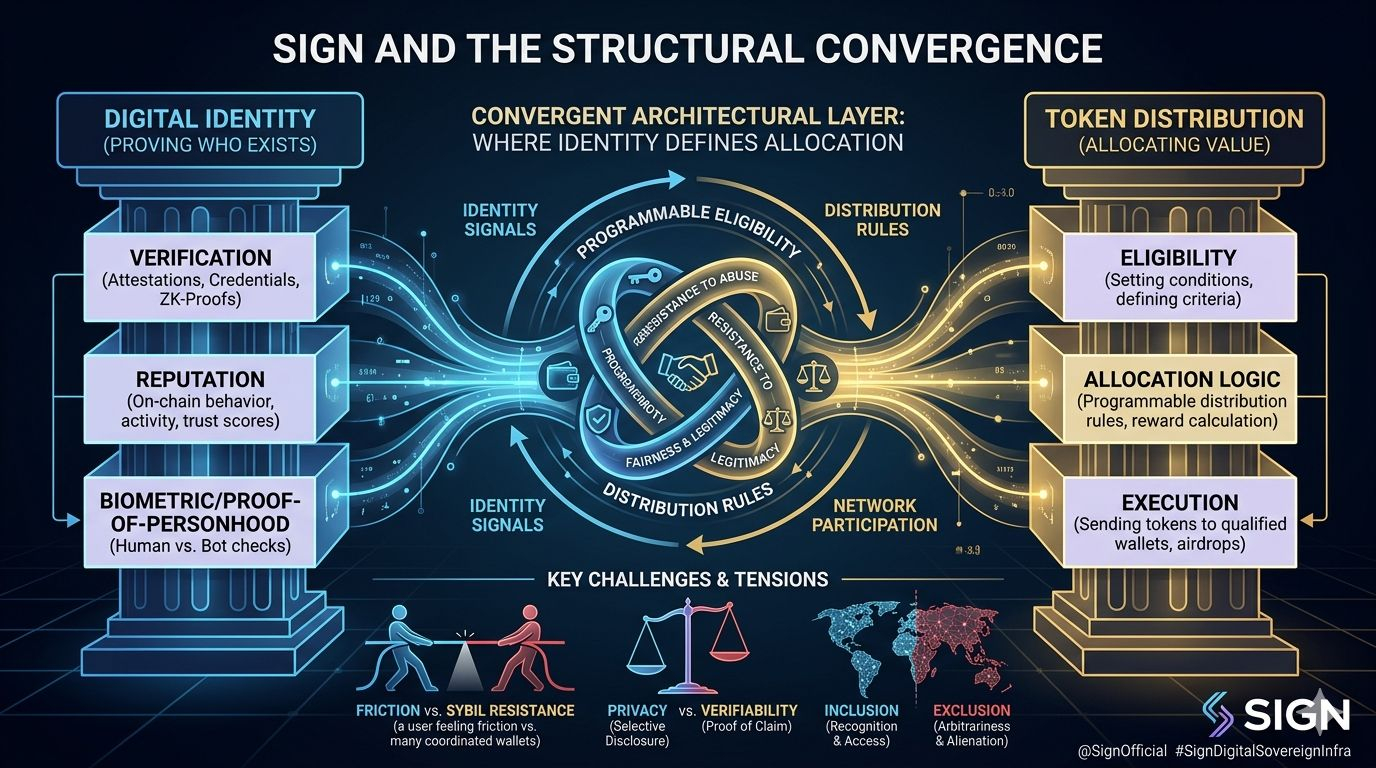
When I look at this space carefully, one shift feels impossible to ignore: digital identity and token distribution are no longer separate systems. They are merging into one architectural layer. And that is not accidental.
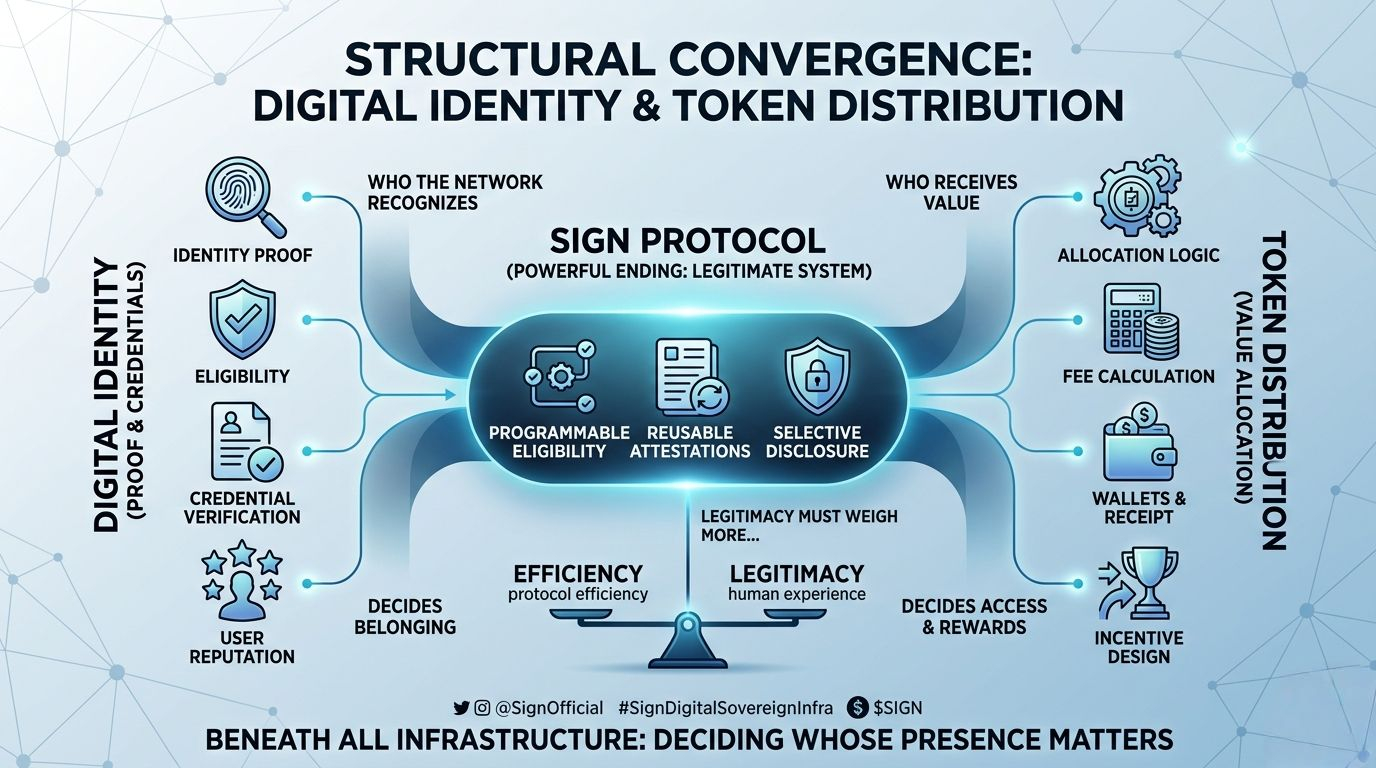
At the surface level, identity proves who someone is, and distribution sends tokens to wallets. But in practice, both answer the same deeper question: who does the network recognize, and who receives value?
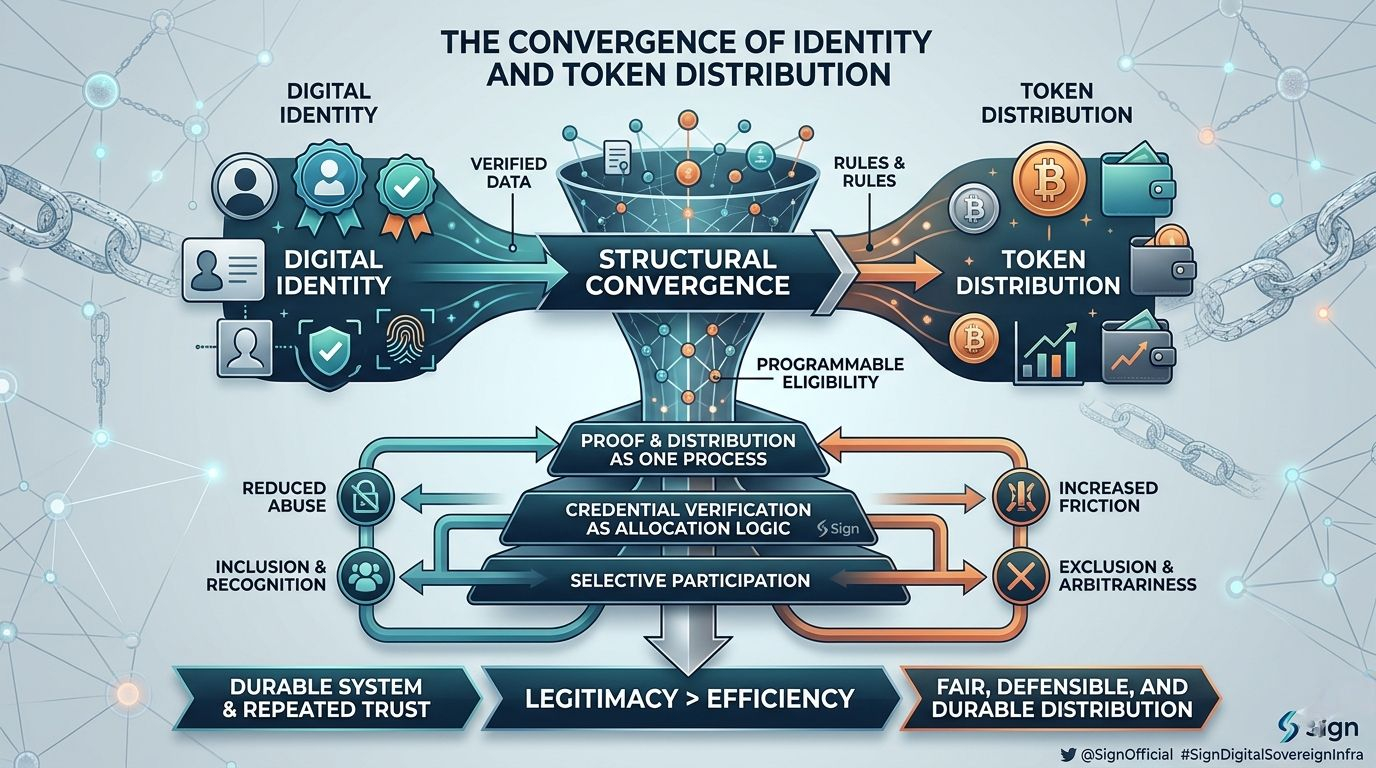
Every token distribution contains judgment. It decides which users qualify, which behaviors count, which wallets are credible, and which participants deserve access. The moment a project defines eligibility, it is already performing identity work even if it avoids calling it that.
This convergence did not happen because it sounds elegant. It happened because distribution became harder.
As token allocations became more valuable, every measurable metric became gameable. Transaction counts were farmed. Volume was manufactured. Wallets were split. Engagement was staged. Loyalty was simulated just long enough to qualify.
Projects learned the hard way that shallow wallet metrics are not enough.
To distribute fairly, a system must distinguish between one real participant and fifty coordinated wallets. It must separate genuine engagement from optimized reward extraction. That pressure naturally pulls distribution toward stronger identity signals.
This is why projects like Sign are strategically important. The framing itself reflects the shift. Credential verification is no longer treated as a side utility it is being embedded directly into allocation logic. Proof and distribution are becoming part of the same process.
We are moving from broad distribution to conditional distribution.
Sending tokens widely is easy. Sending them with logic that feels fair, defensible, and durable is much harder. Projects now want programmable eligibility rules that define who qualifies, why they qualify, and how that decision can be verified later.
That pushes identity toward the center of protocol design.
But this shift carries tension.
Stronger identity layers can reduce abuse, but they also introduce friction. Every verification step creates hesitation. Every new credential requirement changes who continues and who quietly leaves. A system can become more resistant to manipulation while becoming less welcoming to real users.
And distribution is not mechanical. It is emotional.
Inclusion feels like recognition. Exclusion feels personal. If someone participates for months and is filtered out at the end, they do not experience that as elegant incentive design. They experience it as arbitrariness.
Once identity and distribution converge, legitimacy becomes heavier.
Reusable credentials and attestations offer a compelling direction: verify once, reuse across applications, reduce repeated friction, and preserve privacy through selective disclosure. That is real progress.
But portability increases the power of whoever defines the credential schema. Governance, revocation rights, issuer credibility all become structural risk factors. Convenience can reduce friction, but it can also concentrate influence.
This is the deeper tension in the category.
Projects want identity systems portable enough to matter, but not dominant enough to become invisible gatekeepers. They want distribution systems selective enough to resist abuse, but not rigid enough to feel extractive. They want privacy-preserving verification, yet enough certainty to allocate real value.
These goals do not align cleanly.
That is why execution risk here is far higher than it first appears.
This category is not just building infrastructure. It is defining who belongs. It is shaping how networks filter participation and assign value. Every improvement creates second-order effects. Better filtering can reduce abuse but it can also narrow access. Better reputation systems can improve targeting but they can also harden hierarchies.
Long-term relevance will matter more than short-term campaigns.
Anyone can optimize one distribution event. Building a durable system for repeated allocation, repeated participation, and repeated trust is far harder.
The strongest projects will understand that identity is not only a verification problem. It is an incentive design problem, a governance problem, and a behavioral problem. And distribution is not just treasury movement it is a statement of what the network values.
The convergence between identity and token distribution is not a trend. It is a structural necessity.
Blockchain systems have reached a point where value allocation cannot be separated from participant qualification. Networks must decide who can claim, who can receive, who can prove, and who counts and they must do so in a way that users experience as legitimate.
That is the real challenge.
If projects in this category get it right, they can make distribution more credible, resilient, and aligned with contribution. If they get it wrong, they risk building systems that feel efficient from the protocol side but alienating from the human side.
And in the long run, legitimacy will matter more than efficiency.
Because beneath all the infrastructure language, this space is really about one thing:
How a network decides whose presence matters and how that decision turns into access, rewards, and power.
@SignOfficial #SignDigitalSovereignInfra $SIGN
