#SignDigitalSovereignInfra $SIGN @SignOfficial
Nothing breaks when policy changes.
That’s exactly why it’s dangerous.
On Sign, an attestation issued six months ago still resolves today with the same clarity. Same issuer. Same signature. Same schema logic it was created under. You pull it through SignScan and it looks just as clean as anything issued this morning. No warnings. No decay. No visual hint that the meaning behind it has already shifted somewhere else.
And yeah… that’s the part people trust a little too easily.
Because policy doesn’t live inside the attestation. It never really did. It sits outside it, moves separately, gets rewritten in quiet ways that never fully reflect back onto what’s already been issued. So now you end up with two versions of truth running side by side — one that still verifies perfectly, and one that actually defines what should be allowed now.
Same record. Different meaning.
Most systems don’t know how to deal with that. They aren’t built to ask what this approval meant at the time. They just check if it still passes. And on Sign, it almost always does. That single check becomes the whole decision, even when it shouldn’t.
Feels efficient.
Also where it starts slipping.
A dataset gets pulled. Schema matches. Wallet type matches. Program label looks close enough. Nobody really wants to slow down and split hairs over when this approval was issued or what rules were active back then. It all just gets grouped, passed forward, treated like one clean population.
And that “close enough” logic… that’s doing more damage than it looks like.
Because the system isn’t failing. It’s doing exactly what it was designed to do — reduce everything into something actionable. Eligible or not. Included or excluded. There’s no room in that compression for policy timelines or shifting intent.
So old approvals keep moving forward.
A wallet that passed under lighter checks suddenly shows up in a stricter phase. Residency wasn’t required then. Sanctions maybe weren’t refreshed. Maybe the second layer of verification didn’t even exist yet. None of that shows up anymore. All that survives is the clean record.
And that’s enough for the system.
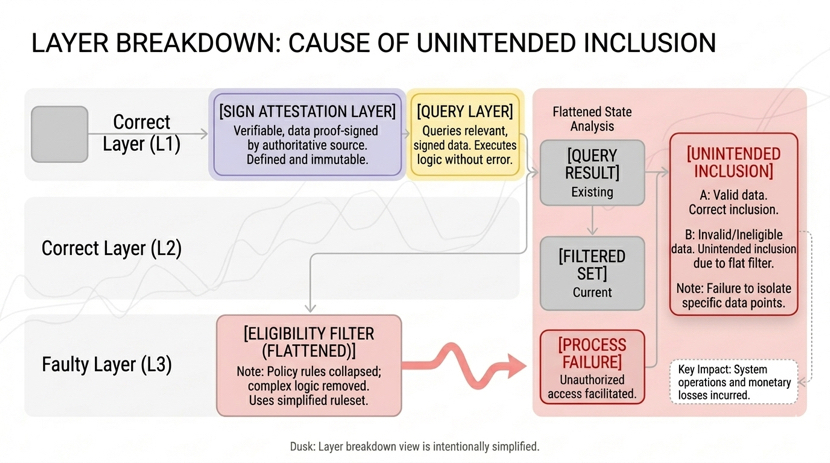
This is the uncomfortable part. Every layer looks right when you isolate it. Sign did its job. Query returns exactly what exists. Filters process what they’re given. No bugs. No obvious mistakes. Just a chain of decisions built on assumptions nobody really challenged.
And those assumptions stack quietly.
You don’t notice it immediately. Nothing looks off. Reports come out clean. Numbers line up. Everything feels stable. It’s only when someone traces a specific wallet — one that doesn’t quite belong — that the gap shows itself.
And the explanation always sounds… reasonable.
The attestation was valid.
It resolved correctly.
It matched the schema.
Yeah.
That’s not the question though.
The real question is:
why was it still allowed to matter here
That part usually lands a bit late.
Because systems don’t ask that. People do. And by the time a person is asking, the system has already made the decision. So instead of enforcing intent, everything defaults to structure. And structure has no memory of why rules changed in the first place.
That’s how scope drifts.
Not loudly. Not all at once. Just small overlaps that never get separated properly. The old record stays. The new policy arrives. And somewhere in between, systems quietly decide those two things are compatible.
They’re not.
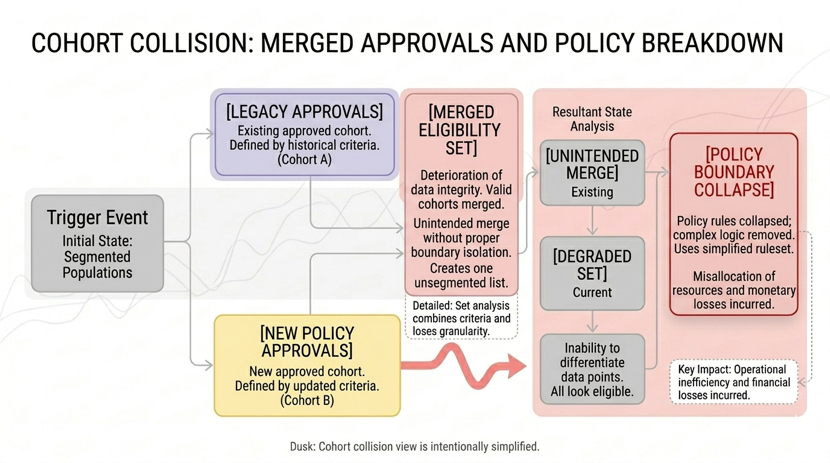
Over time, this starts showing up in places people don’t expect. Eligibility expands without anyone explicitly approving it. Access widens in ways that feel justified because the data supports it. Decisions start leaning on records that were never meant to carry this version of authority.
And the worst part is… it all looks legitimate.
Because Sign never broke.
It did exactly what it promised — preserved truth, made it portable, kept it verifiable. But that preserved truth doesn’t carry its original limits with it. It just shows up, clean and convincing, in places it probably shouldn’t.
That gap is easy to ignore.
Until it isn’t.
Because once old approvals start influencing new outcomes, undoing it isn’t clean. You can’t delete history. You can’t pretend it didn’t happen. You have to go back and teach systems how to read it properly — split cohorts, tighten filters, actually respect when something was issued and why.
That’s heavier than most teams expect.
So they delay it.
And things keep running.
Until one day the numbers are right, the data is valid, everything checks out… and the outcome still feels wrong.
That’s usually the moment it clicks.
Nobody was actually checking the meaning anymore.
Sign keeps everything resolving.
That’s the strength.
But once policy moves on, that same strength turns into pressure. Because now the system has to decide what still counts and what doesn’t — and most of them were never really built for that kind of judgment.
They just keep moving.
And eventually…
so does the mistake.
#SignDigitalSovereignInfra $SIGN
