
When I was browsing Binance Square today, I saw something quite 'real': the platform directly provided a wave of incentives for the CreatorPad event with SIGN, from 2026-03-19 to 2026-04-02. The reward pool clearly states 1,968,000 SIGN coins, and it's the kind of gameplay where 'tasks are exchanged for tokens'. To put it bluntly, this isn't just the community getting excited; the platform is pulling attention in one direction using traffic and tasks—you may not like it, but it's hard to pretend it doesn't exist.
Guys, let's set aside our emotions for a moment; what I'm more concerned about is: why is it specifically SIGN? You should know, the market isn't lacking new coins; it's lacking infrastructure that is 'implementable, explainable, and can be accepted by the external world.' This set of SIGN, if only considered as 'identity', 'airdrop', or 'token issuance tool', I think you'll miss the point; it resembles a 'layer of evidence': turning a certain claim, qualification, identity, or compliance result into verifiable, traceable proofs that can be transported between different systems. Understanding it as an on-chain 'notarized document/proof material' will bring you closer to its intended use.
The term geopolitics sounds grand, but when broken down, it is actually quite specific: cross-border business, identity and qualifications, sanctions and compliance, data sovereignty, and the cost of mutual trust between institutions... When these aspects become tense, what gets magnified first is 'Who are you, what qualifications do you have, and are you qualified?' The traditional internet resolves this through platform endorsement, while Web3 addresses it through on-chain assets and signatures. However, in tougher scenarios, simply saying 'I signed' is not enough; you need to prove 'who signed, what was signed, what the basis for signing was, and whether it can be audited afterward.' The SIGN document directly positions it towards a larger narrative: Sovereign Infrastructure, and the examples given are public project qualifications, regulatory thresholds, and judicial/testimonial proofs, which are all 'hard scenarios.' This is very geopolitical: as the world begins to fragment, trust will break into many small islands, and infrastructure that can reduce trust costs will become more valuable.
Let me present the 'coin' aspect again, or else I might be accused of only discussing ideals without mentioning prices. According to Binance's real-time price page, the current price of SIGN is about 0.03 USD, with approximately 1.6 billion in circulation, a 24-hour trading volume of about 30 million USD, and a market cap in the range of over 50 million USD. Can you say it is very strong? Not really; but can you say it is not played by anyone? Data does not support that. This level is both awkward and very real: it is neither at the point of 'liquidity everywhere' in a big market nor is it 'air with no one to take it over' stagnant water; it is more like waiting for a clearer external catalyst.
Looking at the supply structure, the figure given by Cmc is a total of 10 billion, with about 16.4% in circulation, and the FDV is around 300 million USD. The significance of this structure is straightforward: there is still a long supply story to tell. Prices cannot just be viewed as 'hot or not'; you must consider the unlocking, distribution, and actual consumption capacity of the ecosystem together, otherwise, it is easy to encounter the awkward situation of 'the narrative was correct, the price also went up, but the supply pushed you back.'
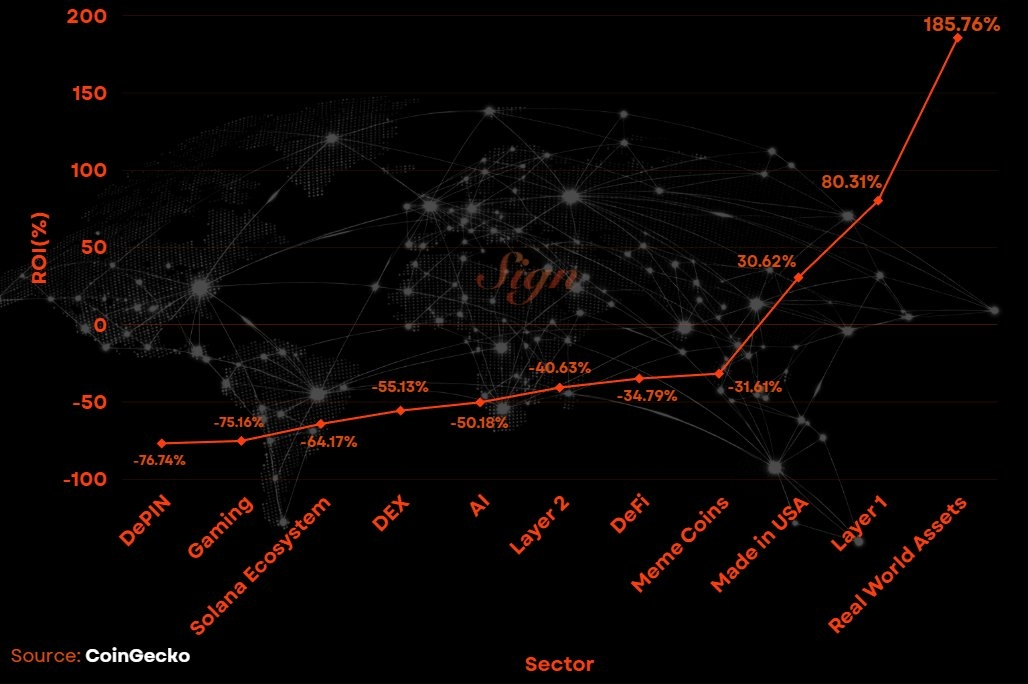
My somewhat 'cold' judgment on SIGN is: its track is not sexy, but it can easily be dragged along by the real world. Identity, proof, qualifications, compliance—these are often mocked in bull markets for lacking 'imagination,' but once the macro environment tightens, regulatory and cross-border frictions increase, and platforms and institutions become more afraid of taking the blame, everyone is more willing to spend money on 'verifiable.' You can see that much of the current on-chain growth is essentially 'moving offline trust online'; previously, it was about transactions, now it is about qualifications and evidence. The SIGN attestation model essentially packages 'declaration + issuer + verifiability' and allows it to flow across systems. If it can successfully navigate several high-frequency scenarios, such as qualification proofs for platform tasks, anti-cheat proofs for airdrops, institutional access proofs, or even tougher 'compliance threshold proofs,' then it is not just a single-point product, but will become a foundational component for many businesses.

Here I must admit a hesitation of my own: for something like a proof layer, the biggest fear is 'technically feasible, but commercially unnecessary.' Because many scenarios can be sufficiently handled with centralized databases, which are even cheaper and faster. For SIGN to win, it must present reasons that demonstrate 'this is the only way.' For example, collaboration costs across platforms, chains, and institutions; the need for platforms to conduct large-scale activities while fearing witch attacks; regulatory demands for auditing trails; and the need for certain qualification proofs to have traceable, verifiable, revocable, or updatable mechanisms (even revocation must leave a trace). These are the hard logic for the existence of on-chain evidence layers; otherwise, it will become 'very beautiful, but optional.'
Bringing the perspective back to the label of 'geopolitical infrastructure,' I prefer to view SIGN as a 'trust interface standard.' The essence of geopolitics is the fragmentation of rules; once fragmented, mutual trust becomes the most valuable. When mutual trust becomes expensive to a certain extent, people will be willing to use technology to make mutual trust cheaper. The previous internet made communication cheaper, and now it seems to be making 'evidence and qualifications' cheaper. You can imagine that in the future, many 'regional rules/industry rules/platform rules' will emerge, and each set of rules will require a verifiable pass. Whoever can provide a universal, composable, and auditable pass foundation is more likely to meet long-term demand. SIGN chooses to speak very directly: targeting larger, harder 'sovereign/institutional needs.' This path is difficult, but once successfully navigated, the barriers will be even stronger.
From the perspective of 'life-saving priority,' how would I keep an eye on this? I will not tell you to buy or sell here; I will only discuss three real matters I will monitor. First, can the trading volume and depth maintain a decent range—currently around 30 million USD in 24 hours, which at least indicates that there are still people willing to exchange chips; if later the enthusiasm drops to 'only small amounts,' then you need to be very careful. Second, is the ecosystem 'consuming proof' rather than 'talking proof'—that is, how many real businesses are using this attestation system, rather than just publishing a few articles? Third, be aware of the selling pressure expectations brought by the supply rhythm; you need to keep the total of 10 billion and the circulation ratio in mind, otherwise, it is easy to ignore that 'there is still inventory' when emotions run high.
Finally, I want to conclude with a phrase that may not sound pleasant but is very practical: projects like SIGN are best suited to test whether you are 'only chasing bullish narratives.' Because it does not rely on stories to explode; it relies on the fact that 'the real world is becoming increasingly distrustful of each other' to push forward. If it succeeds, looking back, you will find it is not because the community narrative was written beautifully, but because many businesses genuinely need an auditable evidence layer; if it fails, it is likely not due to technology, but because the real world does not need it that much, or has been taken over by cheaper centralized solutions. I will regard it as a long-term observation line: when it is hot, do not rush to chase it; when it is cold, do not rush to mock it; the key is whether it can turn 'proof' into a repeatedly invoked infrastructure.

